Security Operation Centre (SOC)
Importance for Business

In today’s world of cyberattacks and data breaches, organisations of all sizes need to prioritise the protection of technology assets. However, many organisations cannot afford to hire a full-time in-house IT security team due to budget constraints and competing priorities. A wise solution to this problem is to partner with a SOC or a security operations centre. SOC is an outsourced service that performs traffic flow analysis and monitoring threats and attacks.
In this article, we invite you to understand the basic features of SOC and their roles in helping companies to protect their data.
Table of content:
What does a Security Operations Centre do?
The Security Operations Centre (SOC) is a team of IT security professionals who monitor the entire IT infrastructure of an organisation 24 hours a day, 7 days a week. They are responsible for detecting cybersecurity events in real-time and will respond as quickly and effectively as possible.
The SOC also selects, operates, and maintains your organisation’s cybersecurity technologies and continuously analyses threat data to find ways to improve your organisation’s security regime.
SOC can help the organisation to integrate and coordinate your organisation’s security tools, practices, and security incident response. This usually leads to improved precautions and security policies, faster threat detection, faster response to security threats, greater effectiveness, and lower costs. SOC can also increase customer trust and simplify and enhance corporate compliance with industry, national, and global data protection regulations.
Why is SOC Important?
With the increasing amount of cyberattacks across the globe, it has become crucial to follow the latest website security trends in the market to keep your business cyber safe. Providing excellent security requires an in-depth understanding of your business. It not only just scans for an attack but can act against a threat. Your IT team might be too busy to be watching your systems constantly. They have other tasks to attend to, so they may not respond to threats until there’s an alarm.
The Benefit of Using Security Operations Centre to Protect Data
In theory, an organisation can effectively protect itself without a dedicated SOC. However, in reality, this is complex and error-prone, and businesses remain vulnerable to cyber threats. Dedicated SOCs bring several benefits to your organisation, including continuous network protection, threats response and prevention, reduced cybersecurity costs, and improved collaboration.
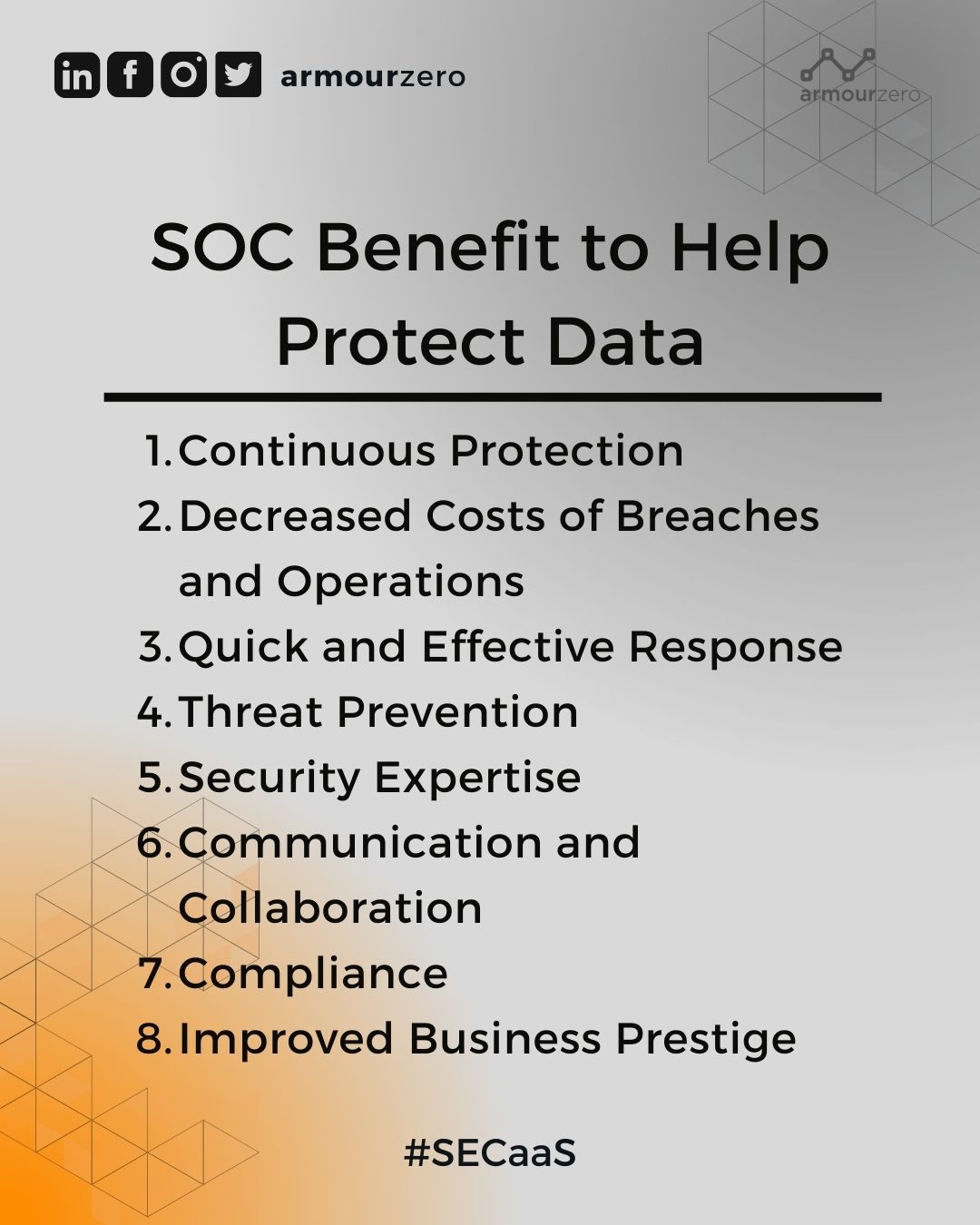
1. Continuous Protection
Security operations centres run 24/7 year-round.
2. Decreased Costs of Breaches and Operations
By minimising the time a cyberattacker lurks in an enterprise’s network, the SOC team can reduce the effect of a violation.
3. Quick and Effective Response
Because SOC team members continuously monitor for threats.
4. Threat Prevention
The analysis and threat hunting conducted by SOC teams help prevent attacks from occurring in the first place.
5. Security Expertise
A security operations centre often consists of a SOC manager, incident responder and security analyst(s), as well as other specialised positions, such as security engineers, threat hunters, forensic investigators and compliance auditors.
6. Communication and Collaboration
A SOC team is well versed in communication and collaboration
7. Compliance
Key SOC monitoring capabilities are integral to enterprise compliance, especially following regulations that require particular security monitoring functions and mechanisms, such as GDPR.
8. Improved Business Prestige
Having a SOC indicates to employees, customers, and stakeholders that the company takes data security and privacy seriously. This helps businesses, employees, and customers feel more comfortable sharing data. The more seriously a company takes the protection and confidentiality of its data, the greater trust it will earn from its constituents.
How does SOC Work?
The number of SOC teams depends on the size of the organisation and the industry, but most teams have similar roles and responsibilities. SOC is a centralised feature within an organisation that uses people, processes, and technology to prevent, detect, analyse, and respond to cybersecurity incidents while continuously monitoring and improving the organisation’s security regime.
The SOC is an example of a Software as a Service (SaaS) model because it operates in the cloud as a subscription service. In this context, it provides the layers of expertise employed in your organisation’s cybersecurity strategy and operates 24/7 to ensure that your network and endpoints are constantly monitored. SOC works with the onsite IT team to address the issue and investigate the root cause if a vulnerability or an incident is found.
Security Operations Centre’s Main Functionality
The main task of the SOC is to protect the organisation from cyber-attacks. The SOC team needs to perform several tasks to manage security incidents effectively. ArmourZero is providing SOC to complete their SECaaS system. Here are 3 main functionality of ArmourZero’s Security Operation Centre (SOC):
1. Real-time monitoring, prevention, detection, and recovery by dedicated SOC analyst
ArmourZero in-house SOC analyst team to learn about your business and actively monitor for any unusual activity according to your nature of business. This includes blocking attacks from spreading across your IT network by immediately cutting off an infected computer by isolating it from the network.
Here’s the list of our offerings:
- 24/7 Rapid Detection & Response Management
- 24/7 Incident Alert Escalation & Monitoring
- 24/7 Global Threat Notification
- The monthly Analysis Report (MAR) was provided to review the protection summary for the month.
- Host isolation and response
- Incident management – Complete with Root Cause Analysis (RCA)
- Actively review and analysis of Phishing email, Spam, and Shadow IT for Email Protection Service
- Security alerts to all clients indicating that threats might have infiltrated their environment. (e.g., phishing, malware, suspicious activity)
2. Accessibility – anytime and anywhere 24/7/365
We built an in-app Change Request feature, so you could easily reach out to our SOC analyst anytime and anywhere. This can ensure a quick and timely response to your queries, system updates, and incidents.
This includes:
- Troubleshooting/enquiry of product issue
- Changes of configuration
- Changes (addition/removal/modification of policy)
- Whitelist/blacklist of website access
3. Fast response and unlimited support
Ensuring a quick and timely response is always our priority. Therefore, we commit to responding to SLA within an hour for your queries, policy changes, and incidents. Not to mention, the support provided is also unlimited.
Find out more about ArmourZero’s service here.
![]()
Written by:
Bernadetta Septarini (Content Marketing). Experienced content marketing and social media in the information technology and services industry.
Share this post
Related Posts

Earth Day: The Connection of Cybersecurity and Sustainability
- 22 Apr 2024
- By:Fanny Fajarianti
- Category: ArmourHacks
Uncover the link between Earth Day and Cybersecurity, promoting sustainability through data protection and environmental stewardship. Let’s secure a greener future.

What is DevSecOps? Definition & Best Practices for Tech Industries
- 18 Apr 2024
- By:Bernadetta Septarini
- Category: ArmourHacks
Learn about DevSecOps, principles, and best practices for the tech industry. Integrate security seamlessly into software development and enhance quality.

Safeguarding Your Organisation During the Hari Raya Holiday
- 09 Apr 2024
- By:Bernadetta Septarini
- Category: ArmourHacks
Protect your organisation from holiday cyberattacks during Hari Raya. Learn more about the risks and best practices for holiday security with ArmourZero.

Cyberattacks: A Growing Threat to Higher Education
- 02 Apr 2024
- By:Fanny Fajarianti
- Category: ArmourHacks
Universities hold sensitive data but face cyberattack risks in the digital age. Explore the impact of cyberattack and learn how to protect your institution.

