Beware of Scare Software
aka Scareware
All humans make mistakes and that is a fact of life and we know the majority of all security incidents involve human error. Many of these are successful security attacks from external attackers who prey on human weakness in order to lure insiders or outsiders within organisations to unwittingly provide them with access to sensitive information.
Such a human frailty brings to my last and final article for this blog, the topic of Scare Software aka Scareware.
Together with my partner-in-crime, my co-blog author, Encik (Mr.) TS Saiful Bakhtiar (who has written his last and final article prior), we are moving onto bigger and better things to explore in our respective careers’ and lives’ journeys.
Let us delve a wee bit further what scareware is. Scareware is a social engineering technique aimed to scare the victim into believing they have a virus on their device and should buy or download specific software. It is based on human emotions as it is used to scare someone and trick them into downloading malware. Scareware, which is a combination of the words “scare” and “software” plays on human emotions and reactions.
As addicted internet users that many of us are, we would have seen pop-ups, in various forms, on our screens saying something like “Warning! Virus Alert!” or “Warning! 5 Virus Detected!”, that is, dear readers, scareware in action. The main intention of scareware is to convince the user through fear that their device is infected with a virus (or several) and that they should take immediate action and download or purchase the malicious software.
However, unlike baiting, which promises to reward the user, scareware looks to build anxiety and fear to manipulate users. Also, unlike smishing, which spreads via SMS, scareware works across devices and on both desktop and mobile.
5 Characteristics of Scareware
As stated, Scareware typically comes in the form of a pop-up that is made to look like it came from a software company, and the 5 common red flags are;
- It comes from a software company you have never heard of.
- Somehow, the software has already scanned your device and detected all these viruses.
- Best of luck to closing the pop-up window, as the closing button (X) is either well-hidden or hovering over the mouse close to it, will open a new pop-up over the previous.
- You have to act fast and there is usually a big red button (sometimes flashing, just in case you’ve missed it somehow) that will tell you to download now!
- The pop-up headline will always be something like Warning! or Virus Detected!
Method to Spot Scareware
Knowing how to spot scareware is the 1st step in avoiding it:
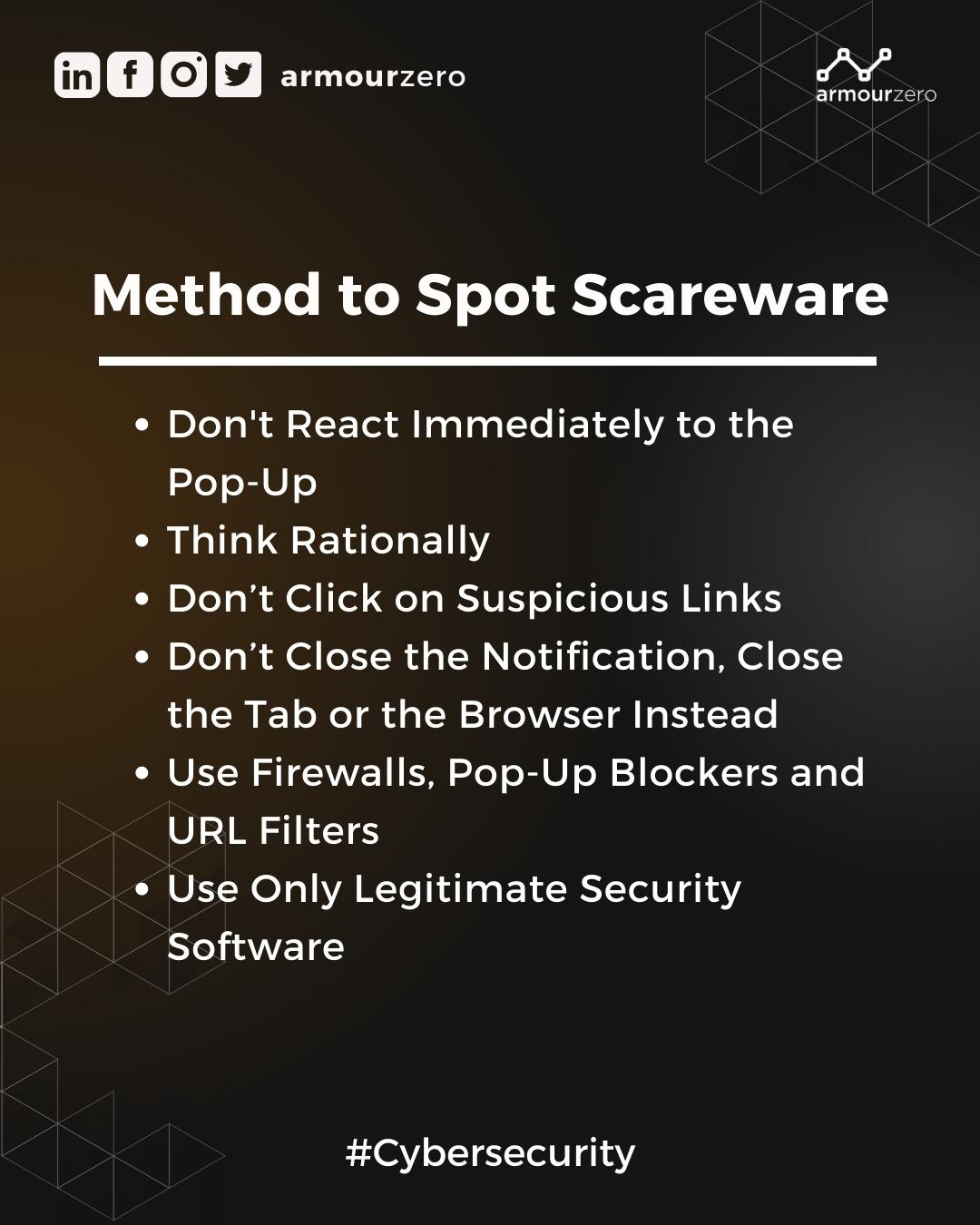
1. Don’t React Immediately to the Pop-Up
Attackers play on one’s emotions and use scare tactics to manipulate the victim into making a hasty decision. They will also do another social engineering attack, called whaling. Do not react immediately. Instead, take a deep breath and slow down.
2. Think Rationally
Read between the lines. There is much more to the warning that pops up on the screen than meets the eye. For example, have you ever heard of this particular software security before? Know that legitimate companies like Norton, Kaspersky, and others will never ever send scareware. Also, how is it possible that they already scanned your device and detected those viruses if you never interacted with them or their software in the 1st place? Usually, one has to download the antivirus software on one’s device and give permission to scan for malicious software. Even then, a virus scan can take anywhere from a few minutes (for a quick scan) up to several hours, sometimes (for a full scan).
3. Don’t Click on Suspicious Links
Do not click on a button or a link just because it says click me!. If one is unfamiliar with the company or the URL looks suspicious, it will likely lead you to a malicious website or download infected software onto your device.
4. Don’t Close the Notification, Close the Tab or the Browser Instead
Lots of scareware pop-ups use a fake Close or X button that clicking on will actually download malware on one’s device instead of closing it. This is called Clickjacking. To avoid this, close the tab with the pop-up or even the entire browser instead.
5. Use Firewalls, Pop-Up Blockers and URL Filters
Use these 3 to stop pop-ups from appearing on one’s screen and facilitate the social engineering attack.
6. Use Only Legitimate Security Software
Last but not least, legitimate security software companies will never send pop-ups like these, even more so if one is not their user. Use trusted antivirus software to regularly scan and remove viruses from one’s device instead of believing that a random pop-up magically detected a virus (or several) on it.
In conclusion, like many social engineering attacks, scareware is also trying to manipulate users into making panicked and urgent actions. Educating oneself is the key to recognising those techniques.
Always trust only legitimate security programs and companies which support end-to-end encryption and 2FA (2 Factors Authentication). Know how to protect one’s computer and data from hackers. As emails are the perfect getaway for hackers, registering with a secure and private email provider is the 1st step to regain the security and privacy one deserves.
Read more here for When Expert Meets Expert articles by Eugene Chung.
Share this post
Related Posts

Cybersecurity: Achieving the ‘Hole-in-One’ of Digital Defence
- 07 Nov 2023
- By:Bernadetta Septarini
- Category: When Experts Meet Experts (WEME)
Discover the connection between cybersecurity and sports with Tony Smith, Regional VP at WithSecure. Let’s achieve the ‘Hole-in-One’ of Digital Defense.

Job Hunting Tips for IT Graduates
- 14 Nov 2022
- By:Ts. Saiful Bakhtiar Osman
- Category: When Experts Meet Experts (WEME)
The job market is tough and competitive. Learn some tips on how to do job hunting for IT graduates from ArmourZero’s mentor and expert Ts. Saiful Bakhtiar.

Tips to Successfully Sell a Credible Cybersecurity Solution
- 07 Nov 2022
- By:Eugene Chung
- Category: When Experts Meet Experts (WEME)
How do Cybersecurity sales convince prospects to trust their services and/or products? Learn more about it from ArmourZero’s mentor and expert Eugene Chung.

IT Leadership – A Tribute to My Mentor
- 31 Oct 2022
- By:Ts. Saiful Bakhtiar Osman
- Category: When Experts Meet Experts (WEME)
This article is a tribute to the late Encik Mohd Izzanee Idris, a Boss and Mentor that taught IT Leadership for ArmourZero’s mentor Ts. Saiful Bakhtiar.

