How to Protect Your Business
From Email Phishing

Phishing is the act of sending an email that falsely claims to be from a legitimate organisation and is usually combined with a threat or request for information. For example, an account will close, a balance is due, or information is missing from an account. Then, the email sender will ask to give confidential information such as bank account details, PINs, or passwords that will be used by the sender to conduct fraud. Phishing attacks continue to become more sophisticated with targeted attacks giving a threat to many businesses.
According to APWG (Anti-Phishing Working Group) Phishing Attack Trend Report Q4 2021, phishing attacks hit an all-time high in APWG’s reporting history with 316,747 attacks in December 2021. This number of attacks has become more than three times as common as early 2020.
Furthermore, the 2021 report also shows a growing trend of phishing attacks against cryptocurrency companies, which inched up to 6.5% of all attacks. Also, the financial sector was the most frequently victimised by phishing in Q4, with 23.2% of all attacks. Attacks against SaaS and webmail providers continued to be numerous.
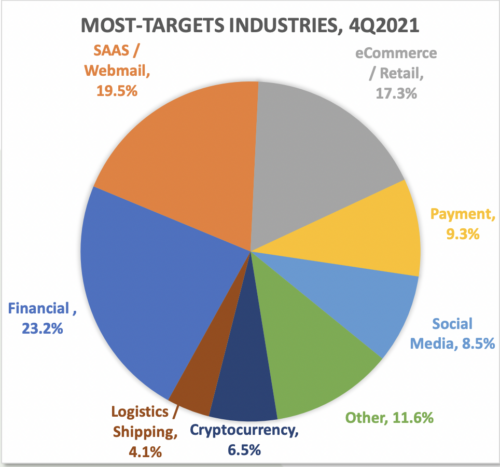
Most target industries for phishing attacks in 2021. Source: APWG Report Q4 – 2021
Examples of Email Phishing (with images)
96% of phishing attacks arrive by email, 3% are through malicious websites, and 1% via phone. When it’s done over the phone, it is called vishing (voice phishing), and smishing (SMS phishing) when it’s done by text message. Therefore, to protect your business from email phishing, it is needed to detect a phishing email. Based on IT Governance UK Blog, there are several ways to recognise email phishing, for example:
1. The message is sent from a public email domain
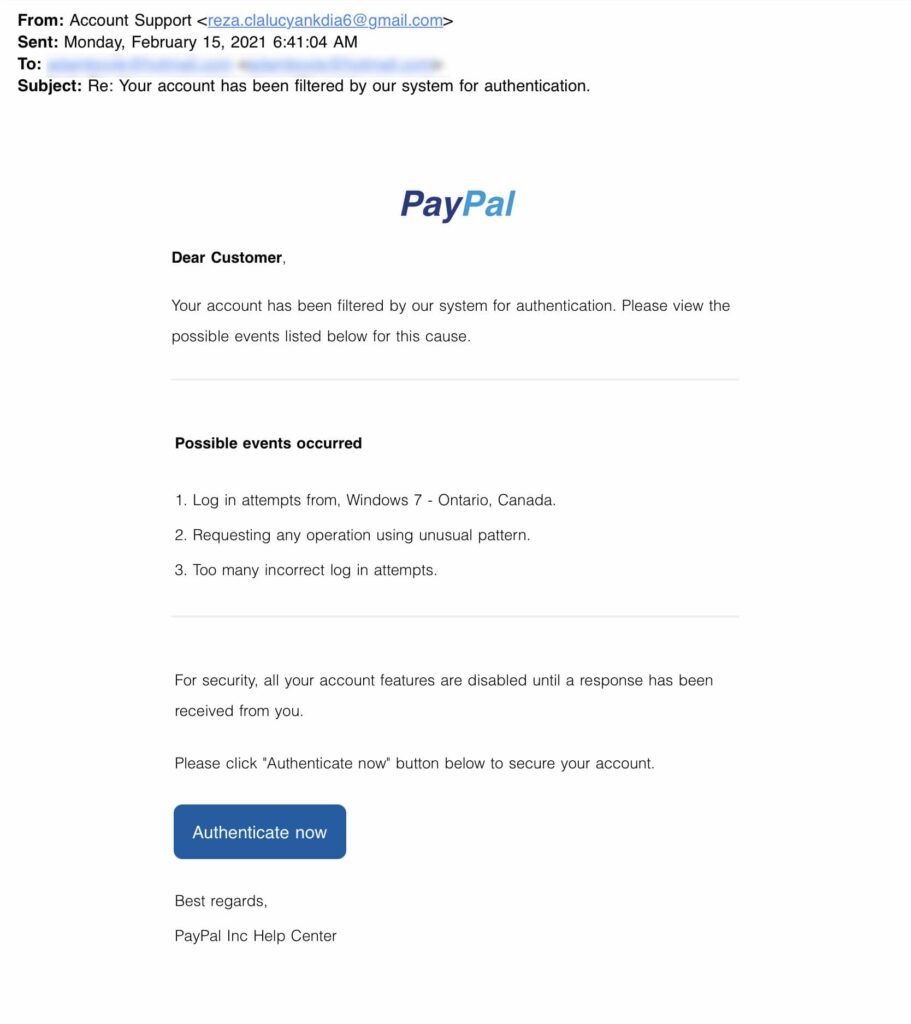
Source: Pickr
One of the most obvious ways to spot scam email is if the sender uses a public email domain, such as ‘@gmail.com’, ‘@yahoo.com’, ‘@outlook.com’, etc, because most companies and organisations these days will have their own email domain and company accounts. In this example, the sender appears to be from PayPal under the “Account Support” name but if you check the recipient email address, it uses a free public domain ‘@gmail.com’.
Some sophisticated approach is by including the organisation’s name as part of the domain, for example ‘[email protected]’. At first glance, it seems like a legit email address because it has the word ‘PayPal’, but it is pretty much impossible for a huge company such as PayPal to use free email from Google.
2. The domain name is misspelt
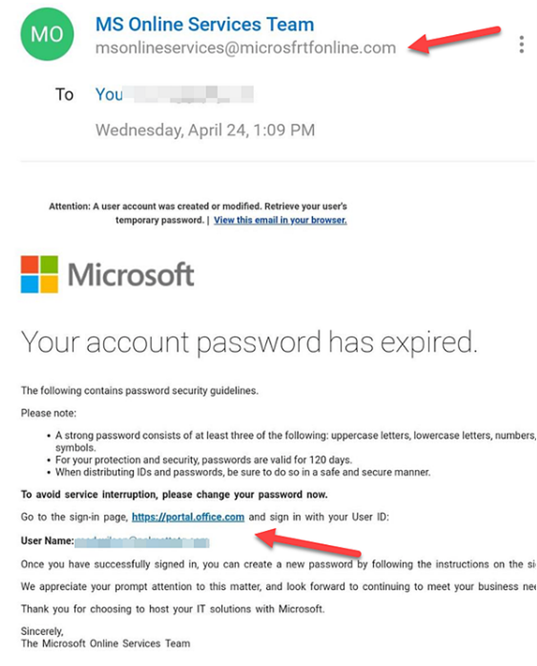
Source: GoPTG
In contrast with previous way to spot email phishing, this time the email address is not from a free account such as ‘@gmail.com’, but has a “valid” domain name. Nowadays, it is easy to buy a domain name from a registrar. In this example, the scammer has registered the domain ‘microsfrtonline.com’ which can be seen as ‘microsoft online’ at glance. Therefore, we need to carefully check the spelling of the email address.
3. The email is poorly written
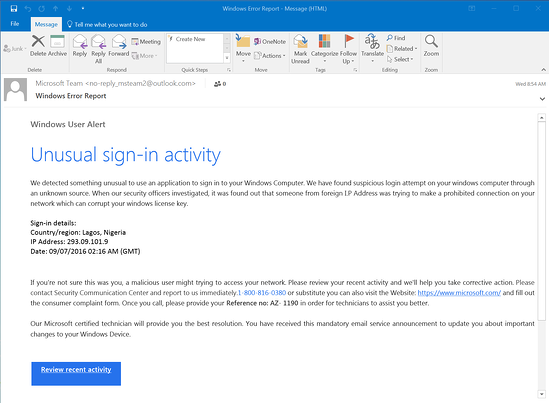
Source: KNOWBE4
Why are so many phishing emails poorly written?
It is because most scammers are not very good at writing and many of them are from non-English-speaking countries. So, when they create phishing messages, scammers will often use a spellchecker or translation machine, which will give them all the right words but not necessarily in the proper context.
From the example above, there are strings of missed words, such as in “a malicious user might be trying to access” and “Please contact Security Communication Centre”. These are consistent with the kinds of mistakes people make when learning English. Any supposedly official message that’s written this way is almost certainly a scam.
With this in mind, it becomes a lot easier to spot the difference between a typo made by a legitimate sender and a scam.
4. It includes infected attachments or suspicious links
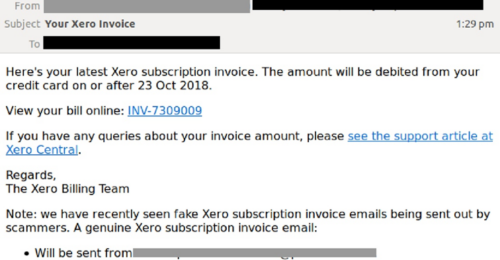
Source: MailGuard
Like the example above, the scammer claims to be sending an invoice with an infected attachment and links. When the recipient opens the attachment, they will see that the invoice is not for them. The attachment unleashes malware on the victim’s computer that can perform any malicious activities and might harm the business.
Therefore, never open an attachment unless you are fully confident that the message is from a legitimate party. Although, you should look out and check carefully for anything suspicious in the attachment.
5. The message creates a sense of urgency
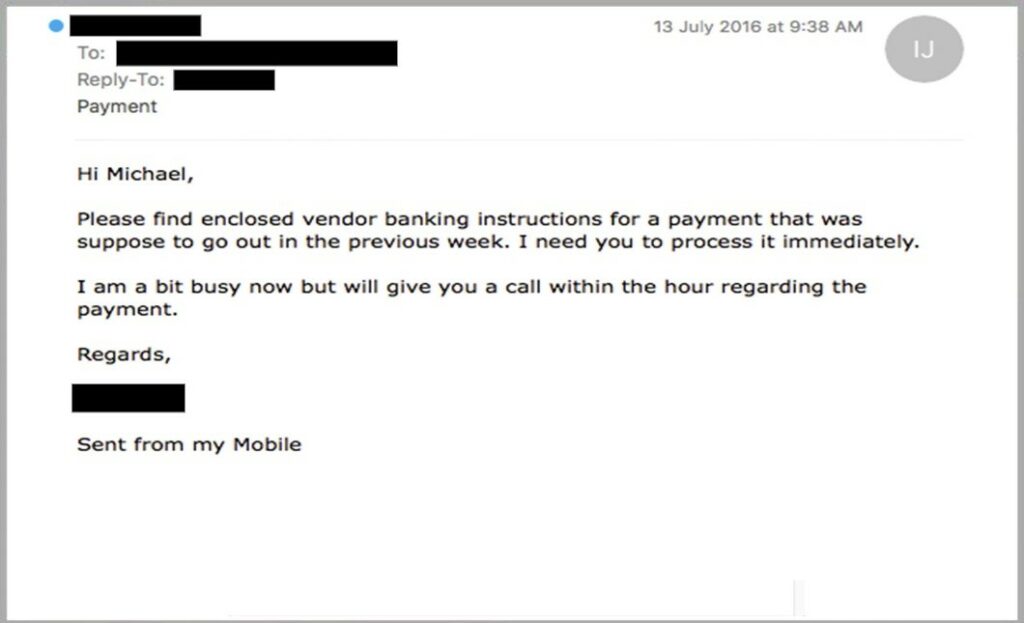
Source: MailGuard
The cyber criminals know that we are going to pay more attention if our boss or senior colleagues send us an email with a vital request. So, in email phishing the sense of urgency is manufactured because the scammers understand it will be effective in a workplace.
That’s why so many scams request that you act now or else it will be too late. This has been evident in every example we have used so far.
How to protect your business from phishing
Since the impact of phishing attacks for business can be severe to business, it is important to learn how to combat the threat of phishing. Several tips to prevent email phishing:
- Provide regular staff with awareness training to identify and prevent email scams.
- Carefully examine the email address, URL, and spelling used in any correspondence.
- Be careful what you download. Never open an email attachment from someone you don’t know, and be wary of email attachments forwarded to you.
- Be especially wary if the requestor is pressing you to act quickly. These are several words that are often used by the scammers: Urgent, Request, Important, Payment, Attention.
- Use cybersecurity solutions that give email protection that leverages internal context, AI, and a trusted reputation network unique to a company and can prevent email phishing attacks.
ArmourZero provides Email Protection as-a-Service powered by Avanan, the best breed of Email Security Solutions, with only US$6.00/user/month or US$60/user/year we are able to prevent delivery of malicious emails to inbox, protect Microsoft 365 and Google Workspace email, account takeover prevention, etc. Book your demo now.
![]()
Written by:
Fanny Fajarianti (Performance Marketing). Experienced digital marketer in the information technology and services industry.
Share this post
Subscribe
Related Posts

Why Security Needs to Move Into Your Applications
- 12 May 2026
- By:Bernadetta Septarini
- Category: ArmourHacks
Discover why compliance alone is not enough for modern cybersecurity. Learn how SBOM visibility helps organisations manage application risk and build cyber resilience.

APAC Regulations Are Raising the Bar on Software Risk
- 22 Apr 2026
- By:Sean Woo
- Category: ArmourHacks
APAC regulations are pushing deeper software risk visibility. Learn how SBOM helps organisations meet compliance and manage vulnerabilities faster.

Why SBOM is Becoming Essential for Organisations in APAC
- 09 Apr 2026
- By:Bernadetta Septarini
- Category: ArmourHacks
SBOM is becoming essential in APAC. Learn how regulation, supply chain pressure, and risk visibility are driving adoption across organisations.

Application Security Checklist for 2026
- 26 Mar 2026
- By:Outman Ardy Yudha
- Category: ArmourHacks
Application security checklist for developers and security teams, covering best practices, vulnerability management, and continuous protection.
