How Secure is the Cloud
vs
How to Use the Cloud Securely?
- Published: 11 Jul 2022
- By: Ts. Saiful Bakhtiar Osman
- Category: When Experts Meet Experts (WEME)

This week’s article is the continuation of my previous article on Cloud Backup vs Conventional Backup. If you still remember, I did mention in a few of my articles on the question, “How secure is the Cloud?”. This is indeed the question asked by many CIOs and Management who are still not convinced to take this leap and move to Cloud.
Industry Standards and Regularisation
The Cloud is no longer an unchartered place or full of the unknown. We have International Standards and continuous Governance at a country level and globally. There are independent bodies which were set up to promote and provide guidelines for Cloud Service Providers to comply to ensure that all these players provide the best and the most secured services.
-
Cloud Security Alliance (CSA)
One of the key independent organisations that I want to highlight is the Cloud Security Alliance (CSA). CSA is the world’s leading organisation dedicated to defining and raising awareness of best practices to help ensure a secure cloud computing environment. CSA has been involved actively to come out with the framework for Cloud cybersecurity control.
The CSA Cloud Controls Matrix (CCM) is a cybersecurity control framework for cloud computing. It is composed of 197 control objectives that are structured in 17 domains covering all key aspects of cloud technology. It can be used as a tool for the systematic assessment of cloud implementation and provides guidance on which security controls should be implemented by which actor within the cloud supply chain. The controls framework is aligned to the CSA Security Guidance for Cloud Computing and is considered a de-facto standard for cloud security assurance and compliance.
CSA also certifies the Cloud Service Provider as proof that the Cloud Service Provider is complying and implementing the Cloud Controls Matrix (CCM). The Security, Trust, Assurance, and Risk (STAR) Registry is a publicly accessible registry that documents the security and privacy controls provided by popular cloud computing offerings.
STAR encompasses the key principles of transparency, rigorous auditing, and harmonisation of standards outlined in the Cloud Controls Matrix (CCM). Publishing to the registry allows Cloud Service Providers to show current and potential customers their security and compliance posture, including the regulations, standards, and frameworks they adhere to. Hence, you as a customer would rest assured that you are getting trusted and secured Cloud services.
More detailed explanations and readings are available on CSA’s website Cloud Security Alliance.
-
ISO/IEC 27017
This standard was published by the International Organisation for Standardisation (ISO) and the International Electrotechnical Commission (IEC) under the joint ISO and IEC subcommittee. This International Standard provides guidelines supporting the implementation of information security controls for cloud service customers, who implements the controls, and cloud service providers to support the implementations of those controls. The selection of appropriate information security controls and the application of the implementation guidance provided, will depend on a risk assessment and any legal, contractual, regulatory, or other cloud-sector specific information security requirements.
Hence, if the Cloud Service Provider is a Certified ISO/ISE 27017, that means that they are complying and your rights are protected, including the following additional 7 security controls:
- Who is responsible for what between the cloud service provider and the cloud customer.
- The removal or return of assets at the end of a contract.
- Protection and separation of the customer’s virtual environment.
- Virtual machine configuration.
- Administrative operations and procedures associated with the cloud environment.
- Cloud customer monitoring of activity.
- Virtual and cloud network environment alignment
All the Cloud Service Providers will be competing to adopt and practise the highest standard as per ISO/ISE 27017, to gain the advantage over their competitors in the market. At the end of the day, we as Customers would be on the winning end. You may find the complete 37 Controls breakdown for ISO/ISE 27017 on the ISO website (document needs to be purchased) and the summary on Wikipedia as follows:
ISO Standard and ISO/IEC 27017 – Wikipedia.
-
Country Specific Regulations and Control
The rapid growth of Cloud technology has forced all the countries to come out with clear guidelines and controls so that their businesses would not be left out of engaging this new technology whilst the national interests are protected. Some countries mandated that the Cloud Service Provider apply for the licence before operating in their country. Some would mobilise their own local tech companies to come out with these Cloud Services and limit the entry of international providers to protect their local players.
Whatever the controls are, this is your assurance that your interest is protected by all parties, and it is secured to engage the Cloud Services. For example, some of these big Cloud Service Providers carry Impact Level 5 (IL5) or/and Impact Level 6 (IL6) endorsement by the Department of Defence (DoD) of the United States. What does that mean? It means that apart from the Military Cloud, these civilian Clouds have been approved as secured and in compliance with the highest IT Security Standards.
The National Institute of Standard and Technology (NIST), under the U.S Department of Commerce, is also another effective governance body that produces a lot of control frameworks, and the standards are acceptable and practised globally. The Cloud Service Providers must adhere to these frameworks to be operating in the U.S and the same level of standards are applied to all their customers around the world. You would be able to check the list of global and local compliance that your potential Cloud Service Provider has from their website and these certifications could be cross-reference with the governance body that issued the respective certifications.
Hybrid Cryptography for System Protection
This is another factor worth highlighting. Cloud Service Providers are using Hybrid Cryptography to enhance the safety of your data in the Cloud. This is a method for securely storing files in the cloud using a hybrid cryptography algorithm. In this system, the user can store the file safely in online Cloud Storage as these files will be stored in encrypted form in the cloud and only the authorised user has access to their files. This also includes the Data-in-transit and Data-at-rest which confirms End-to-end encryption (E2EE). Data-in-transit is data that is moving between endpoints whilst Data-at-rest is sensitive data you store in corporate IT structures such as servers, disks, or cloud storage services.
An encryption algorithm is a method used to transform data into ciphertext. An algorithm will use the encryption key to alter the data in a predictable way, so that even though the encrypted data will appear random, it can be turned back into plaintext by using the decryption key. Hybrid cryptography takes the advantage of integrating more than one cryptographic algorithm to enhance the overall security and performance.
This is where the advantage of going to Cloud would be apparent. Can you imagine how much of a technology investment you would require having a similar setup like this should we be hosting on-premise. Another advantage is we as the customer are leveraging on the robust R&D being done by the Cloud Service Provided for them to provide the best services for all their customers across the globe.
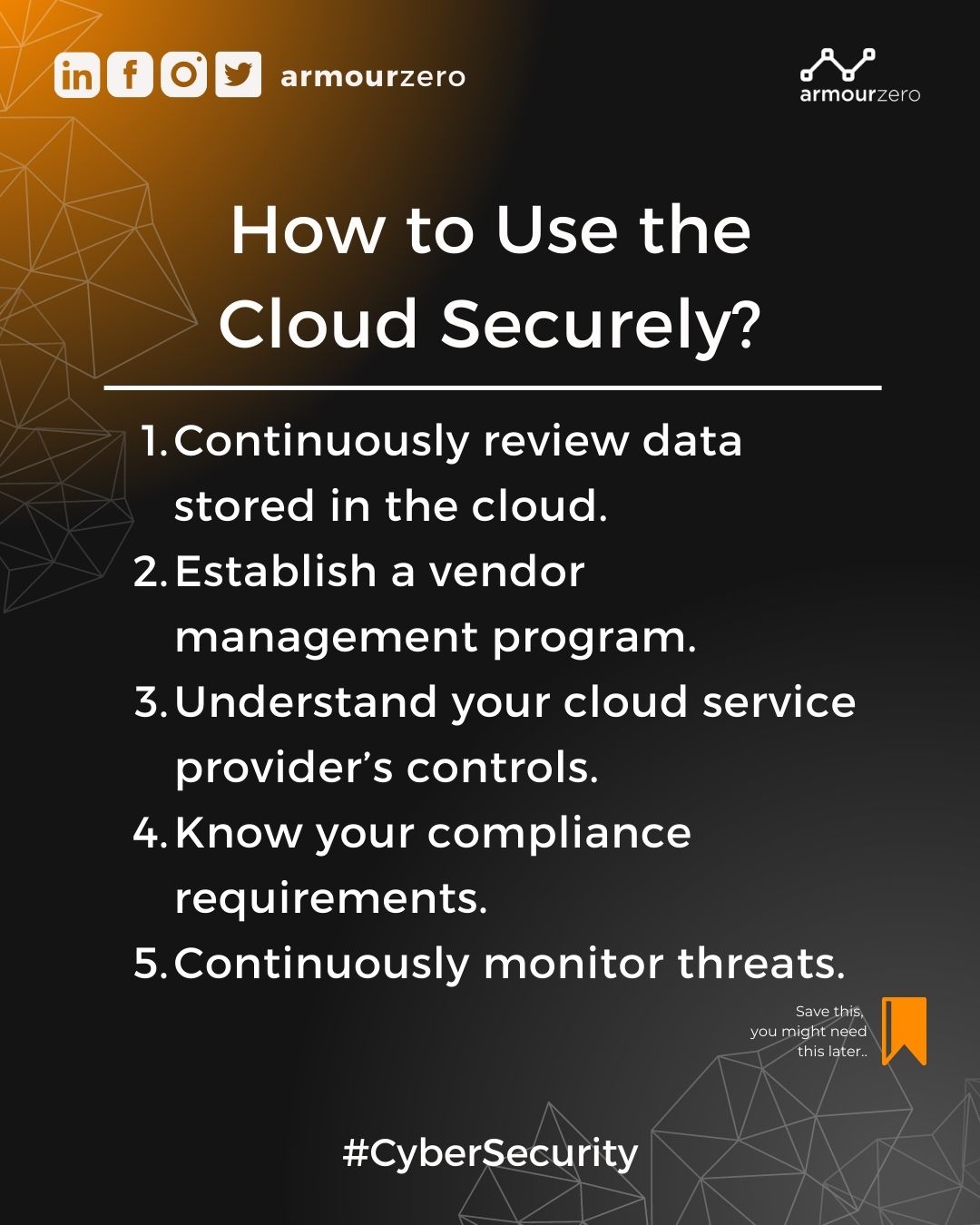
How to Use the Cloud Securely
Even though the Cloud is secured, that does not mean we should sit down and do nothing. Organisations also need to reinforce their internal process to match the new infrastructure that we engaged with. Here are a few good pointers which I extracted from Reciprocity’s page, on continuous monitoring in Cloud:
-
Continuously review data stored in the cloud
Although you don’t control everything within your cloud environment, you can maintain review over the information stored there. You need to review your cloud server regularly to make sure no out-of-scope critical or protected data resides there.
-
Establish a vendor management program
Cloud service providers are vendors. You not only need to trust them, but you need to verify their security controls to protect yourself from data breaches. You need to establish agreed-upon controls and service level agreements with cloud service providers and any vendors whose APIs you use.
-
Understand your cloud service provider’s controls
Whether it’s using a public cloud or hybrid cloud, your service provider is going to be storing and transmitting your data. You need to assure that the cloud provider incorporates an appropriate level of protection over that data. Unfortunately, even though you’re contracting with the cloud service provider, you own the data at risk.
It’s important to understand how your service provider encrypts data and controls access and authentication. You also need to know its incident response plans.
-
Know your compliance requirements
If you need to comply with the EU General Data Protection Regulation (GDPR), you need to make sure your cloud service provider offers local data centres.
If you need to report data breaches under a regulatory requirement, you need to assure that your cloud services provider will keep you informed so that you can stay compliant.
-
Continuously monitor threats
In the same way that you monitor your data environment, you need to monitor the continuously evolving security risks to your cloud infrastructures, including cyberattacks.
The primary concern over engaging a hybrid cloud infrastructure is lack of visibility into who accesses all the points of entry. Unfortunately, while others maintain controls, you’re ultimately responsible for any data breaches arising out of your third-party vendors, including your cloud providers.
You can have further readings from Cloud Security vs. Traditional Security — Reciprocity.
Start with good planning…
We are already at the end of this week’s article. Did I manage to convince you, or at least change your perception of Cloud? Whatever the decision is, always start with good planning. Do not go into Cloud just simply for the sake of following the trend, or because everyone else is going into Cloud. You would know your organisation the best. Conduct your Risk Assessment properly and work with Top Management to agree on a realistic ROI from this investment. Good luck!
Catch When Expert Meets Expert by Ts. Saiful Bakhtiar Osman articles every bi-weekly Tuesday. Don’t forget to subscribe to stay connected. You are also encouraged to ask questions and seek advice from him.
Share this post
Related Posts

Cybersecurity: Achieving the ‘Hole-in-One’ of Digital Defence
- 07 Nov 2023
- By:Bernadetta Septarini
- Category: When Experts Meet Experts (WEME)
Discover the connection between cybersecurity and sports with Tony Smith, Regional VP at WithSecure. Let’s achieve the ‘Hole-in-One’ of Digital Defense.

Beware of Scare Software aka Scareware
- 21 Nov 2022
- By:Eugene Chung
- Category: When Experts Meet Experts (WEME)
What is Scare Software or Scareware? Learn more about this Social Engineering technique that aimed to scare the victim with ArmourZero mentor Eugene Chung.

Job Hunting Tips for IT Graduates
- 14 Nov 2022
- By:Ts. Saiful Bakhtiar Osman
- Category: When Experts Meet Experts (WEME)
The job market is tough and competitive. Learn some tips on how to do job hunting for IT graduates from ArmourZero’s mentor and expert Ts. Saiful Bakhtiar.

Tips to Successfully Sell a Credible Cybersecurity Solution
- 07 Nov 2022
- By:Eugene Chung
- Category: When Experts Meet Experts (WEME)
How do Cybersecurity sales convince prospects to trust their services and/or products? Learn more about it from ArmourZero’s mentor and expert Eugene Chung.

