The Future and
Importance of Cybersecurity

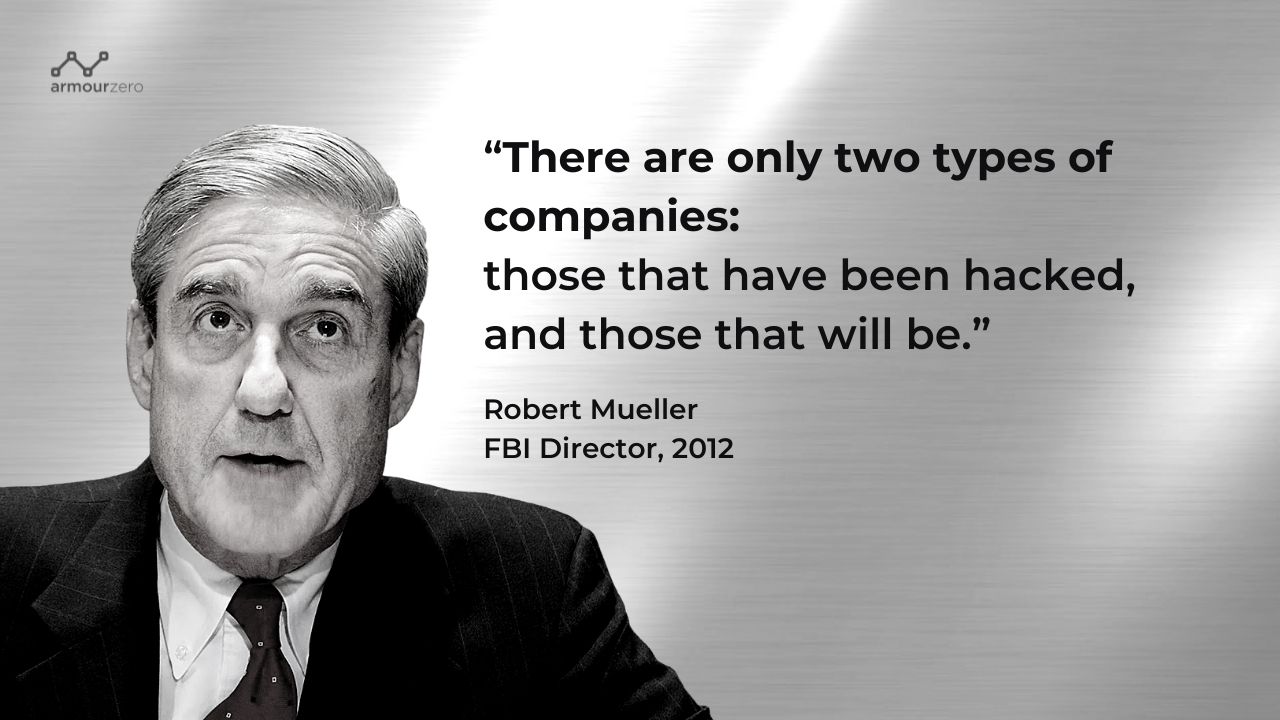
Lately, I have been pondering about this next big wave, Cybersecurity. The International Data Corporation (IDC) forecasted that worldwide cybersecurity spending will reach approximately USD$175 billion in 2024, with security services being the largest and fastest growing market segment. The rise in cyberattacks, especially from ransomware, has increased the cyber insurance and cyber protection markets.
Definition
According to any reputable dictionaries, Cy·ber·se·cur·i·ty is the practice of being protected against the criminal or unauthorised use of electronic data, or the measures taken to achieve this.
I like to state that I don’t consider IT Security or Information Security on the same level as Cybersecurity even though you will find even from so called IT security vendors and End Users addressing Cybersecurity on the same breath as IT or Information Security, synonymously.
If you’re in information (data) security, your main concern is protecting your company’s data from unauthorised access of any sort and main concern is for the confidentiality, integrity, and availability of data (this is often referred to as the “CIA”). Most modern business data resides electronically on servers, desktops, laptops, or in the cloud but before all confidential information was migrated online, it was sitting in a filing cabinet. And some confidential information still is. Information (data) security is concerned with making sure data in any form is kept secure.
If you’re in cybersecurity, your main concern is protecting your company’s data from unauthorised electronic access. Cybersecurity involves identifying what the critical data is, where it resides, its risk exposure, and the technology you have to implement in order to protect it.
While cybersecurity deals with protecting the information in cyberspace, information security means protecting the data in cyberspace and beyond. In other words, the Internet or the endpoint device may only be part of the larger picture.
While cybersecurity can be viewed as a subset of information security, ultimately both focus on data protection. Both cybersecurity and information security personnel need to be aware of the scope and the shared mission to secure your enterprise.
Ever heard of the Square and Rectangle argument?
Every square is a rectangle because a square is a quadrilateral with all 4 angles being right angles. Similarly, cybersecurity is a part of the IT security umbrella, along with its counterparts, physical security and information security.
But not every rectangle is a square since the criteria to qualify as a square means all sides must be the same length. The point is, not all IT security measures qualify as cybersecurity, as cybersecurity has its own distinct assets to protect.
The Future of Cybersecurity
From the high-level understanding of what Cybersecurity is, the relevancy and importance of Cybersecurity protection will determine its future. In most if not all business establishments, Cybersecurity is categorised into 5 distinct types:
- Critical infrastructure security
- Application security
- Network security
- Cloud security
- Internet of Things (IoT) security
To cover all of its bases, an organisation should develop a comprehensive plan that includes not only these 5 types of cybersecurity but also the 3 components that play active roles in a cybersecurity posture (PPT):
- People
- Processes
- Technology
We can efficiently streamline processes and utilise the best available technology money can buy BUT people, they are difficult to manage or discipline to adhere to Cybersecurity governance and policies.
Realistically, no matter what precautions you put into place, if people don’t follow the rules, you are still at risk. The saying “you’re only as strong as your weakest link” comes to mind. In most cases, human error is just that, a mistake and big mistakes are costly.
Most people aren’t intentionally bypassing security protocol. They either are not trained to do so or they are not educated about the significance of their actions. Conducting security awareness training and reinforcing the most basic cybersecurity principles with employees outside of the IT department can make a big difference in the company’s security posture.
Why is Cybersecurity important?
Last but not least in respect to the importance of Cybersecurity, the convenience of connected data also means threats from bad actors can do a lot of damage. Examples of bad actors:
- Black hat hackers – the stereotypical bad actor
- Script kiddies – novice hackers
- Hacktivists – security actors who aim to use their powers for good
- Organised crime hackers
- Insider actors gone rogue
Cybersecurity initiatives are essential to protecting our data.
Let us now consider (what) the future of Cybersecurity. Here’s an interesting article to read:
The Future of Cybersecurity: What Will it Look Like in 2031?
Cybersecurity is an ever-growing industry that is developing and evolving to protect individuals and organisations from cyberattacks.
In all practicality, the future of Cybersecurity surely must depend on People and Skill sets. Any organisations implementing strong defences against cyberattacks need skilled and experienced cybersecurity workforce which is not easy to find, considering the large demand. The number of individuals interested in taking courses in cybersecurity is increasing and this trend is expected to grow even more in the future, as the demand is much higher than the supply. If left unattended, cyberattacks will continually increase and become more dangerous. This can be prevented by making continual significant investments in people and by hiring cybersecurity experts or by training employees in cybersecurity related courses.
Conclusion
Cybersecurity is one of the most important aspects of the fast-paced growing digital world. The threats of it are hard to deny, so it is crucial to learn how to defend from them and teach others how to do it too.
Catch When Expert Meets Expert by Eugene Chung articles every bi-weekly Tuesday. Don’t forget to subscribe to stay connected. You are also encouraged to ask questions and seek advice from him.
Share this post
Subscribe
Related Posts

Cybersecurity: Achieving the ‘Hole-in-One’ of Digital Defence
- 07 Nov 2023
- By:Bernadetta Septarini
- Category: When Experts Meet Experts (WEME)
Discover the connection between cybersecurity and sports with Tony Smith, Regional VP at WithSecure. Let’s achieve the ‘Hole-in-One’ of Digital Defense.

Beware of Scare Software aka Scareware
- 21 Nov 2022
- By:Eugene Chung
- Category: When Experts Meet Experts (WEME)
What is Scare Software or Scareware? Learn more about this Social Engineering technique that aimed to scare the victim with ArmourZero mentor Eugene Chung.

Job Hunting Tips for IT Graduates
- 14 Nov 2022
- By:Ts. Saiful Bakhtiar Osman
- Category: When Experts Meet Experts (WEME)
The job market is tough and competitive. Learn some tips on how to do job hunting for IT graduates from ArmourZero’s mentor and expert Ts. Saiful Bakhtiar.

Tips to Successfully Sell a Credible Cybersecurity Solution
- 07 Nov 2022
- By:Eugene Chung
- Category: When Experts Meet Experts (WEME)
How do Cybersecurity sales convince prospects to trust their services and/or products? Learn more about it from ArmourZero’s mentor and expert Eugene Chung.
