Stay Phish-Free: A Guide
to a Safe Online Shopping & Banking

In today’s digital age, online shopping and banking have become an integral part of our daily lives, offering unparalleled convenience. However, with this convenience comes the need for heightened vigilance, as the digital realm can sometimes be fraught with unexpected risks.
Recent cases in Indonesia, involving fraud and deception, have underscored the importance of vigilance in the digital realm. Customers have reported receiving WhatsApp messages from individuals posing as Banking Administrators, who claim a transaction fee adjustment and urge customers to make payments while soliciting sensitive information. (Read more at Finansial Bisnis)
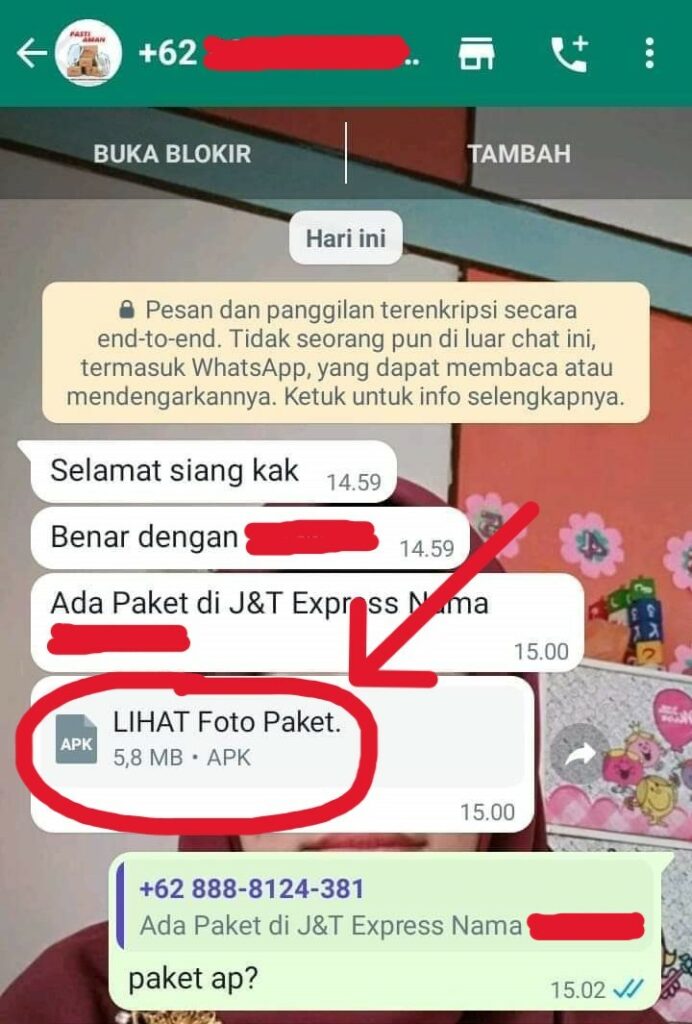
Courier Impersonation Scam Alert in Indonesia
In tandem with these troubling developments, the world of online shopping faces its own set of challenges. Some unscrupulous sellers, regrettably, fall short of delivering on their promises, leaving customers disappointed and financially inconvenienced. (Read more at AsiaOne)
Adding to the complexity, there have been reports of fraudsters impersonating couriers and delivering what seems like a standard package in Indonesia. However, they slyly hand over a seemingly harmless receipt file in APK format, which, unbeknown to the recipient, is an app designed to steal personal data. This clever ruse underscores the importance of staying vigilant in the digital landscape. (Read more at Bank Indonesia)
In this article, we embark on a journey to explore these pressing issues and equip you with strategies to ensure security in your online shopping and banking experiences.
Recognising Phishing Attacks
Phishing attacks are elaborate schemes employed by cybercriminals who impersonate credible and trustworthy entities in an attempt to deceive individuals into disclosing sensitive information. These attacks can take various forms and often manifest through deceptive emails, messages, or websites.
To shield yourself from falling victim to such fraudulent tactics, it’s crucial to be well-versed in recognising the telltale signs of phishing attacks. Here are several common indicators that should raise your suspicion:
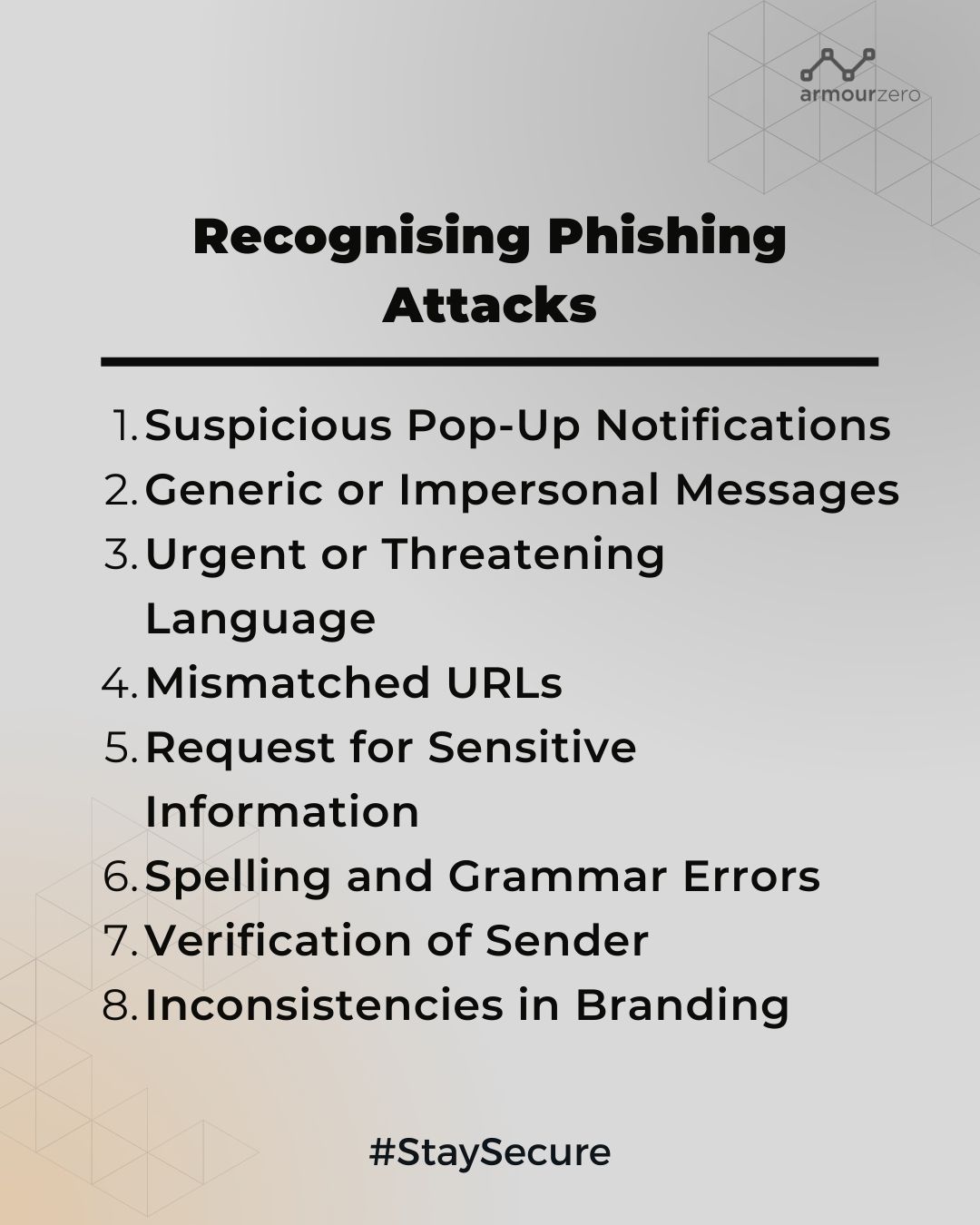
1. Suspicious Pop-Up Notifications or Emails
Be wary that cybercriminals may use these to deceive users into revealing sensitive information, similar to traditional phishing attempts.
2. Generic or Impersonal Messages
Phishing messages, whether via social media, email or even pop-up notifications, often use generic or impersonal greetings rather than addressing you by name.
3. Urgent or Threatening Language
Be cautious of messages that create a sense of urgency, pressure you to act immediately, or threaten consequences if you don’t comply—traits commonly found in phishing tactics.
4. Mismatched URLs
Always check the destination URL by hovering your cursor over links. Cybercriminals typically use misspelled or altered URLs that resemble legitimate sites.
5. Request for Sensitive Information
Avoid providing personal information, such as login credentials, credit card numbers, or Social Security numbers, in response to unsolicited messages or pop-ups.
6. Spelling and Grammar Errors
Look out for noticeable language errors, misspellings, or awkward phrasing, as these are telltale signs of a phishing attempt, whether in social media, emails or pop-up notifications.
7. Verification of Sender
Always verify the sender’s legitimacy and the source of the message before taking any action. When it comes to online shopping, it’s better to check previous reviews or ask for testimonials before making a decision.
8. Inconsistencies in Branding
Pay attention to inconsistencies in logos, colours, fonts, or branding elements within messages. Legitimate organisations maintain consistent branding, while phishing attempts often display variations.
Safe Online Shopping and Banking Practices
As we navigate the digital landscape, online shopping and banking have revolutionised convenience. Yet, this convenience comes with responsibilities. To safeguard your personal and financial information, adopting safe practices is paramount. Here are essential guidelines for ensuring a secure online shopping and banking experience:
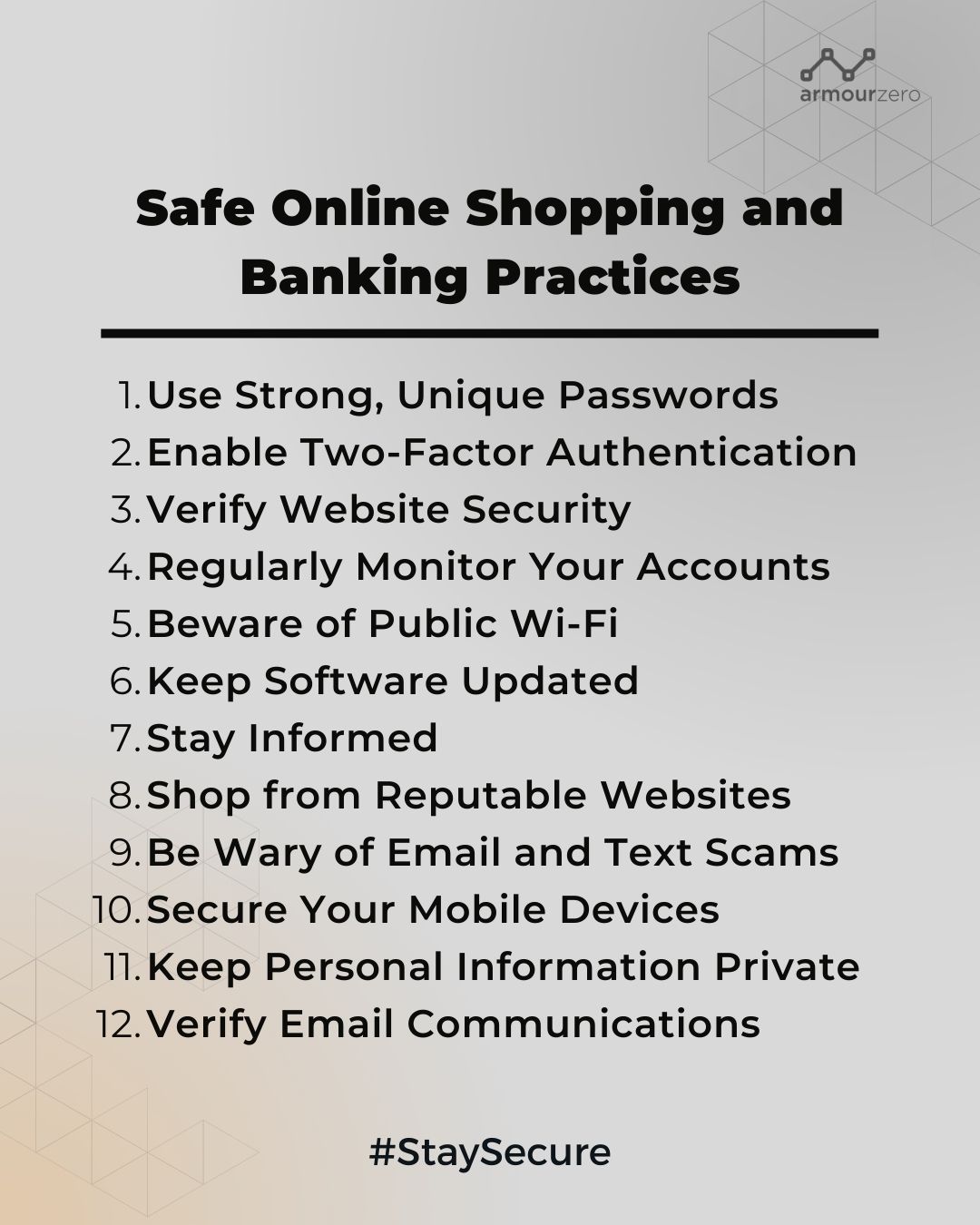
1. Strong, Unique Passwords:
- Craft robust, unique passwords for each online account.
- Consider a trusted password manager to securely store and generate complex passwords.
2. Activate Two-Factor Authentication (2FA):
- Whenever available, enable 2FA for an extra layer of security.
- This commonly involves a secondary verification step, such as a code sent to your mobile device.
3. Verify Website Security:
- Before entering sensitive data, ensure the website is secure. Look for “https://” and a padlock icon in the address bar, indicating a secure connection.
4. Regular Account Monitoring:
- Routinely review your bank and credit card statements.
- Promptly report suspicious activity to your financial institution.
5. Caution on Public Wi-Fi:
- Avoid conducting sensitive transactions on public Wi-Fi networks.
- Unsecured networks can leave your data vulnerable.
6. Keep Software Updated:
- Regularly update your operating system, web browsers, and antivirus software to patch known vulnerabilities.
7. Stay Informed:
- Be vigilant against evolving cybersecurity threats and scams.
- Familiarise yourself with phishing tactics and malware protection.
8. Trustworthy Websites:
- Prefer reputable online retailers and banks.
- Exercise caution with unfamiliar websites.
9. Beware of Email and Text Scams:
- Do not click on links or download attachments from unsolicited emails or text messages.
- These channels are often exploited for phishing attacks.
10. Secure Mobile Devices:
- Apply security features on smartphones and tablets, including encryption, screen locks, and remote tracking capabilities.
11. Guard Personal Information:
- Share personal and financial data only on trusted websites.
- Legitimate organisations do not solicit sensitive information via unsolicited emails or messages.
12. Verify Email Communications:
- Confirm the authenticity of emails from banks or retailers.
- Contact the institution directly through official channels if in doubt.
By adhering to these safe online shopping and banking practices, you fortify your defences against cyber threats. Knowledge and vigilance are your allies in protecting your online transactions and financial well-being.
Conclusion
In conclusion, the digital world offers immense convenience, but it’s crucial to remain vigilant against phishing attacks when engaging in online shopping and banking. By recognising the signs of phishing attempts and following safe practices, you can protect your digital wallet and personal information from cybercriminals, ensuring a safer and more secure online experience.
Safeguarding your business from phishing attacks is easy with ArmourZero. We bundle top-notch email protection, strong endpoint antivirus or endpoint protection with EDR, and seamless patch management into one powerful solution. This all-in-one package shields your business from phishing threats, blocking malicious emails, removing malware, and keeping your systems secure with timely updates. ArmourZero simplifies your defence against phishing, ensuring your data and operations stay safe and sound.
Protect your organisation from cybercrime and cyber threats today with just one click!
See our pricing here and request a demo to understand further.
You can also contact our sales to help you choose the right cybersecurity services for your business.
*This article has been published on e27.co on September 21, 2023
![]()
Written by:
Bernadetta Septarini (Content Marketing). Experienced content marketing and social media in the information technology and services industry.
Share this post
Related Posts

Earth Day: The Connection of Cybersecurity and Sustainability
- 22 Apr 2024
- By:Fanny Fajarianti
- Category: ArmourHacks
Uncover the link between Earth Day and Cybersecurity, promoting sustainability through data protection and environmental stewardship. Let’s secure a greener future.

What is DevSecOps? Definition & Best Practices for Tech Industries
- 18 Apr 2024
- By:Bernadetta Septarini
- Category: ArmourHacks
Learn about DevSecOps, principles, and best practices for the tech industry. Integrate security seamlessly into software development and enhance quality.

Safeguarding Your Organisation During the Hari Raya Holiday
- 09 Apr 2024
- By:Bernadetta Septarini
- Category: ArmourHacks
Protect your organisation from holiday cyberattacks during Hari Raya. Learn more about the risks and best practices for holiday security with ArmourZero.

Cyberattacks: A Growing Threat to Higher Education
- 02 Apr 2024
- By:Fanny Fajarianti
- Category: ArmourHacks
Universities hold sensitive data but face cyberattack risks in the digital age. Explore the impact of cyberattack and learn how to protect your institution.

