In an era where digital landscapes are continually evolving, the need for a robust cybersecurity strategy has never been more critical. Cyber threats are becoming increasingly sophisticated, making it imperative for organisations to adopt comprehensive solutions that go beyond traditional security measures. Unified Threat Monitoring, Management, and Response (UTMMR) emerges as a holistic approach to safeguarding digital assets and ensuring the resilience of business operations.
Understanding Unified Threat Monitoring
Unified Threat Monitoring is the first line of defence in the cybersecurity arsenal. It involves the continuous surveillance and analysis of network activities to identify potential threats and vulnerabilities. By leveraging advanced technologies such as intrusion detection systems, firewalls, and anomaly detection, organisations can gain real-time visibility into their IT environments.
The Role of Unified Threat Management
Unified Threat Management (UTM) consolidates multiple security features into a single, integrated solution. This includes firewall, antivirus, intrusion prevention, content filtering, and more. UTM streamlines security operations, providing a centralised point for monitoring and managing diverse security components. This not only enhances efficiency but also ensures a coordinated response to potential threats.
Implementing a Unified Threat Response Strategy
Once threats are identified through monitoring and management, a prompt and coordinated response is crucial. Unified Threat Response involves implementing automated and manual processes to contain and mitigate security incidents. This may include isolating affected systems, blocking malicious traffic, and deploying patches or updates. The goal is to minimise the impact of an attack and prevent it from spreading further.
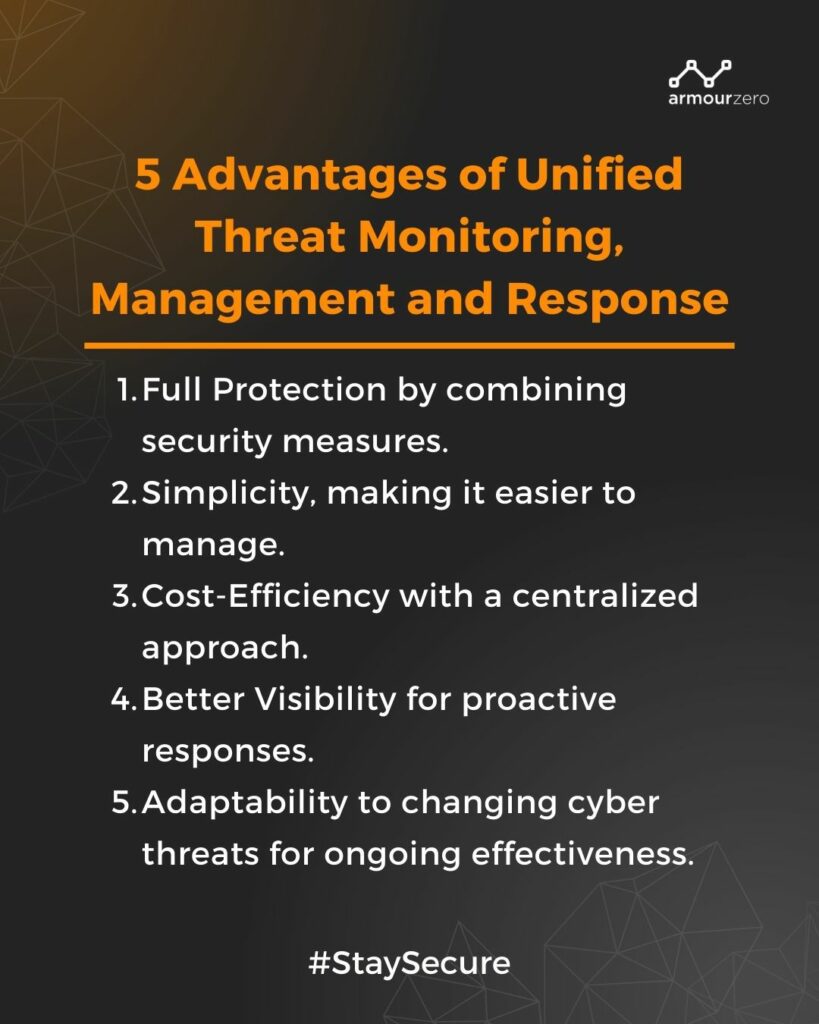
Advantages of Unified Threat Monitoring, Management and Response (UTMMR)
-
Comprehensive Protection
UTMMR offers a comprehensive defence by combining monitoring, management, and response strategies. This ensures that potential threats are not only detected, but also addressed promptly and effectively.
-
Reduced Complexity
Consolidating security measures simplifies the overall cybersecurity infrastructure. This reduction in complexity makes it easier for organisations to manage and maintain their security systems.
-
Cost-Efficiency
UTMMR can save costs by eliminating the need for disparate security solutions. A unified approach allows organisations to optimise their cybersecurity investments and reduce operational expenses.
-
Enhanced Visibility
Real-time monitoring provides organisations with enhanced visibility into their networks, allowing for proactive identification of potential threats before they can cause significant harm.
-
Adaptability
UTMMR solutions are adaptable to evolving cyber threats. As new attack vectors emerge, these solutions can be updated and fine-tuned to address emerging challenges.
Conclusion
Unified Threat Monitoring, Management, and Response (UTMMR) represent a pivotal shift in cybersecurity strategies, moving away from siloed approaches towards a more integrated and proactive defence. As organisations continue to face an ever-changing threat landscape, embracing UTMMR not only strengthens their resilience but also ensures a comprehensive and agile response to the dynamic nature of cyber threats. By adopting a unified approach, businesses can fortify their cybersecurity posture and protect their digital assets in an increasingly interconnected world.
Protect your organisation from cybercrime and cyber threats today with just one click!
See our pricing here and request a demo to understand further.
You can also contact our sales to help you choose the right cybersecurity services for your business.

Written by:
Bernadetta Septarini (Content Marketing). Experienced content marketing and social media in the information technology and services industry.
Share this post
Related Posts

Earth Day: The Connection of Cybersecurity and Sustainability
- 22 Apr 2024
- By:Fanny Fajarianti
- Category: ArmourHacks
Uncover the link between Earth Day and Cybersecurity, promoting sustainability through data protection and environmental stewardship. Let’s secure a greener future.

What is DevSecOps? Definition & Best Practices for Tech Industries
- 18 Apr 2024
- By:Bernadetta Septarini
- Category: ArmourHacks
Learn about DevSecOps, principles, and best practices for the tech industry. Integrate security seamlessly into software development and enhance quality.

Safeguarding Your Organisation During the Hari Raya Holiday
- 09 Apr 2024
- By:Bernadetta Septarini
- Category: ArmourHacks
Protect your organisation from holiday cyberattacks during Hari Raya. Learn more about the risks and best practices for holiday security with ArmourZero.

Cyberattacks: A Growing Threat to Higher Education
- 02 Apr 2024
- By:Fanny Fajarianti
- Category: ArmourHacks
Universities hold sensitive data but face cyberattack risks in the digital age. Explore the impact of cyberattack and learn how to protect your institution.