10 Most Common Cyber Threats &
How to Protect Against Them

Cyber threats are more widespread and pose greater risks to individuals and organisations nowadays. Therefore, understanding the most common cybersecurity threats and knowing how to protect against them is essential to protecting sensitive information and staying safe online. In this article, we will examine the most common cybersecurity threats and provide useful tips and strategies to better protect yourself against them.
What is a Cyber Threat?
A cyber threat is any malicious act or activity that aims to take advantage of weaknesses in computer systems, networks, or digital devices in order to eavesdrop on users, disrupt business, steal confidential data, or harm people. Cyber threats can come in various forms, including malware infections, phishing attacks, ransomware, social engineering, and more.
Cybercriminals frequently carry out these threats by taking advantage of gaps in security defences to further their nefarious ends. Therefore, understanding cyber threats is crucial for individuals and especially organisations to effectively protect their digital assets and mitigate potential risks.
What are the Most Common Types of Cyber Threats?
1. Phishing Attacks
Phishing attacks are a type of cyber attack in which perpetrators use cunning methods to convince victims to divulge private information, including passwords, credit card numbers, and other details. These attacks are typically carried out through deceptive emails, messages, or websites that appear to be from legitimate sources, aiming to steal valuable information or spread malware.
One real-life example of a phishing attack is the “Google Docs” phishing scam that occurred in 2017. In this attack, scammers invited recipients to view a Google Docs document by sending phishing emails that purported to be from a known contact. Users were asked to enter their Google account credentials on a fake Google login page after clicking a link in the email that contained those instructions.
Upon entering their credentials, the attackers gained access to the victims’ Google accounts, allowing them to steal sensitive information, send out more phishing emails, or access other personal accounts linked to the Google account. This attack affected a significant number of users and demonstrated how sophisticated phishing scams can trick even cautious individuals into divulging their login credentials.
2. Malware Infections
Malware infection refers to situations where malicious software, often called malicious software, enters a computer or network with the intent to damage, corrupt, steal data, or gain unauthorised access. Malware comes in many forms, including viruses, worms, Trojans, ransomware, spyware, adware, and more. Malware infections can come from a variety of vectors, such as email attachments, malicious websites, compromised software, or downloadable ads.
Stuxnet is one of the most infamous and sophisticated malware infection attacks in history, discovered in June 2010. Intended to target Iran’s nuclear facilities, this malware exploits several zero-day vulnerabilities in Windows operating systems to infiltrate the company’s control systems that oversee uranium enrichment. Its purpose is to disrupt centrifuges by changing their programmable logic controllers (PLCs). Organised by the United States and Israel, Stuxnet marked a significant change in cyber warfare, demonstrating the ability of highly specialised malware to disrupt critical infrastructure systems. The findings are a reminder of the importance of robust cyber security measures and raise global concerns about the implications of advanced malware targeting critical infrastructure.
3. Ransomware Attacks
A ransomware attack is a type of cyber attack where malicious software is used to hide or encrypt a victim’s data or lock them out of their computer system. The attackers also demand a ransom, usually in cryptocurrency, for providing the release key or restoring access to the data. Ransomware attacks can be disruptive and financially damaging to individuals, businesses, and organisations.
One of the real-life examples of this attack is WannaCry, also known as WCry. WannaCry was a widespread ransomware attack that occurred in May 2017, affecting hundreds of thousands of computers globally. It spreads out of Windows’s disadvantages, using eternal foods of the seller to the seller revealed.
WannaCry is distributed via email or malicious links, hiding the victim’s files after installation. The ransom note shows a ransom note demanding payment in Bitcoin. Due to its ability to spread through networks, it has caused huge problems and financial losses, affecting hospitals, businesses and individuals around the world. Although the Lazarus people are called North Korea, the final identity of the attackers is still uncertain. This attack highlighted the importance of timely updates, data backups, and strong cyber security measures for effective ransomware prevention and response.
4. Social Engineering Attacks
A social engineering attack is a type of cyber attack that manipulates individuals into revealing sensitive information, performing certain actions, or providing unauthorised access to protected systems. These attacks use psychological and emotional factors to trick people into trusting the attacker, often using deception, persuasion, or impersonation.
One of the examples of Social Engineering Attack is Target Data Breach in 2013 where the cyber criminals using spear tactics, the attackers targeted a third-party CVC vendor with malware-laden emails, exploiting user actions to gain access to Target’s network. Once inside, the attackers breached the sales process, taking the payment card data of about 40 million customers and accessing the personal information of another 70 million. The breach resulted in significant financial losses, lawsuits, investigations, and reputational damage to Target, highlighting the importance of cybersecurity awareness and strong defences against social engineering attacks that exploit vulnerabilities. people and trust access to sensitive information.
5. DDoS (Distributed Denial of Service) Attacks
DDoS (Distributed Denial of Service) attacks are cyberattacks that aim to defeat a target system, network, or website by flooding it with traffic from multiple compromised computers or devices, creating a botnet. The high intensity of the attack leads to a denial of service for legitimate users, making the targeted service or website inaccessible. DDoS attacks can be triggered by a variety of methods and can have serious consequences, causing chaos, financial loss and reputational damage.
Example of this attack was in October 2016, a significant real-life DDoS attack targeted Dyn, a domain name system (DNS) service provider, causing widespread outages and disruptions. Attackers use botnets of compromised Internet of Things (IoT) devices with weak credentials to disrupt Dyn’s servers and traffic volumes, blocking legitimate requests and affecting key websites and online services such as Twitter, Reddit, Spotify, GitHub. , on Netflix. Although the motivation behind the attack is unclear, it highlighted the vulnerability of IoT devices and highlighted the need to secure them with strong passwords and regular updates. The incident also highlighted the importance of robust DDoS protection for internet infrastructure providers which is critical to ensuring the stability and availability of internet services.
6. Man-in-the-Middle (MitM) Attacks
Man-in-the-Middle (MitM) attack is a type of cyber attack where an unauthorised person intercepts and can alter communications between two parties who believe they are communicating directly. In a MitM attack, the attacker places himself in private between the sender and the receiver, giving the impression that he is the legitimate agent. This allows the attacker to eavesdrop on communications, steal sensitive information, or manipulate data transmitted without the knowledge of the communicating parties.
MitM attacks can occur in a variety of situations, including public Wi-Fi networks, compromised routers, and unsecured communication channels. They pose a major threat to data security and privacy because they compromise the confidentiality and integrity of sensitive information exchanged between individuals and organisations. The consequences of a successful MitM attack can be dire, resulting in data corruption, financial loss, identity theft and other adverse events.
The example of MiTM attack is in 2017, Equifax experienced a verified data breach, affecting more than 143 million Americans. In response, Equifax launched a website, equifaxsecurity2017.com, enabling customers to check if they were affected by the breach. However, a critical flaw emerged as the website employed a shared SSL certificate for hosting, used by numerous other websites. This opened the door for DNS attacks, where fake websites redirected users to fraudulent pages, and SSL spoofing, allowing attackers to intercept data transmitted through the site. As a consequence, users became vulnerable to potential phishing attempts and data interception, exacerbating the impact of the breach.
7. SQL Injection Attack
SQL Injection (SQLi) Attack is a type of cyber attack that targets web applications utilising SQL databases for data storage. In this attack, malicious actors exploit a vulnerability in the application’s input field, allowing them to inject malicious SQL code into the application’s database queries. The purpose is to manipulate the database to retrieve, modify or delete sensitive information stored there. SQL injection attacks are particularly dangerous because they can lead to unauthorised access, data leakage, and potentially damaging data loss, compromising the privacy, integrity, and availability of application data.
During a SQL Injection attack, the attacker typically identifies input fields, such as login forms or search boxes, that are vulnerable to injection. They then inject malicious code, such as SQL statements, into these fields to exploit weaknesses in the application’s installation process. If the application does not properly sanitise user input and does not optimise or escape special characters, the application’s database may corrupt the SQL code, causing unexpected results. Depending on the severity of the vulnerability and the skill of the attacker, they can extract sensitive data, modify database records, elevate privileges, or even gain full control over the underlying server.
One of the examples of SQLi attacks is the Accellion Attack in December 2020. Accellion is a company known for its File Transfer Appliance (FTA) network device widely used by organisations worldwide to securely transfer large and sensitive files, faced a unique and highly sophisticated attack. Despite being over 20 years old and reaching its end of life, the FTA became the target of this breach, highlighting the importance of retiring outdated products.
The attack on Accellion’s FTA involved a clever combination of SQL injection and operating system command execution techniques. Experts suspect that the hackers behind this attack have affiliations with the financial crimes group FIN11 and the ransomware group Clop, indicating the complexity and coordinated efforts behind the intrusion.
This incident serves as a cautionary example, showcasing that SQL injection is not limited to web applications or services alone. Instead, it can be leveraged to compromise backend systems and facilitate the unauthorised exfiltration of valuable data. This emphasises the significance of maintaining robust security practices, even for legacy systems, to thwart potential breaches and safeguard sensitive information from cyber threats.
Read more: What is SQL (Structured Query Language) Injection?
8. Zero-day Exploits
A zero-day exploit is a type of cyber attack that takes advantage of software vulnerabilities unknown to the software vendor or developer. The term “zero days” refers to the fact that the software vendor does not have zero days to close or fix the vulnerability before malicious actors exploit it. In other words, when a vulnerability is exploited, there are no patches or security updates available to address the vulnerability, which makes it dangerous and difficult to defend against.
Zero-day exploits are highly prized by cybercriminals and sophisticated hacking groups because they offer a significant advantage. Since the vulnerability is unknown to the vendor, it can be used to target systems that are still unprotected and unsecured against the exploit. Once a zero-day vulnerability is discovered and exploited, it can lead to various malicious activities, such as accessing unauthorised systems, stealing sensitive information, launching malware attacks or controlling affected devices. . Governments, intelligence agencies, and other sophisticated organisations are increasingly accumulating sophisticated exploits to carry out targeted attacks, making them a powerful weapon in cyber warfare and cyber espionage.
Example of this cyber attack is called Sony Zero-Day Exploits. In 2014, Sony Pictures Entertainment experienced a significant cyber attack attributed to a group known as Guardians of Peace (GOP). The attack targeted Sony Pictures’ computer systems and resulted in the theft of sensitive data, including confidential emails, employee personal information, and unreleased movies. The attackers then publicly released the stolen data, leading to embarrassing revelations and reputational damage for Sony. While the specific details of the zero-day exploits used in the attack were not publicly disclosed, the incident highlighted the potential damage and disruption that can arise from such attacks. It underscored the importance of robust cybersecurity measures, including timely patching and vulnerability management, to defend against evolving threats, including zero-day exploits.
9. Data Breaches
A data breach is a security incident in which sensitive, confidential, or protected information is accessed, disclosed, or stolen by unauthorised individuals or entities. Data breaches can occur in a variety of ways, such as through cyberattacks, hacking, internal threats, accidental exposure, or physical theft of sensitive data. During a data breach, personal information, financial data, intellectual property, trade secrets or other sensitive information may be compromised. The breach can have serious consequences for individuals and organisations, including identity theft, financial loss, reputational damage and legal costs.
One real-life example of a data breach is the Equifax data breach that occurred in 2017. Equifax, The US major credit reporting agency fell victim to a security breach through a vulnerability in intermediary software. Hackers accessed the data of over 160 million individuals, making it one of the largest identity theft cyber crimes to date. The compromised data included Social Security numbers, birth dates, addresses, and, in some instances, driver’s licence numbers and credit card information.
The consequences of this breach were severe, with reported damages of approximately $700 million to support those affected, along with significant reputational damage and inquiries from congressional authorities, which was highly alarming. The incident highlighted the critical need for robust cybersecurity measures and timely vulnerability patching to safeguard sensitive data and prevent such large-scale cyberattacks in the future.
10. Supply Chain Attacks
Supply chain attacks, also known as third-party attacks, are a type of cyber attack that targets vulnerabilities in the supply chain or third-party vendors associated with an organisation. Instead of directly attacking the target organisation’s systems, the attackers focus on compromising the systems or software of trusted suppliers, partners, or service providers that have access to the target organisation’s network or data.
The objective of supply chain attacks is to gain unauthorised access to the target organisation’s sensitive information, systems, or infrastructure by exploiting the trust placed in their third-party partners. By compromising a trusted supplier or vendor, the attackers can use this as a stepping stone to infiltrate the target organisation’s network, spread malware, steal data, or launch further attacks.
Example of this is SolarWinds’ attack. SolarWinds is a major software company based in Oklahoma that provides system management tools for network and infrastructure monitoring, and other technical services to hundreds of thousands of organisations in the world. One of their products is an IT performance monitoring system called Orion that has privileged access to IT systems to obtain log and system performance data.
In 2020, a Russian espionage (hacking group) managed to compromise the supply chain of SolarWind and insert malware into Orion latest software updates. In this case, it meant that the attacker had potential access to the almost 18,000 SolarWind customers, including Microsoft, US Justice Department, State Department, or even NASA.
Learn More: What is Supply Chain Attack?
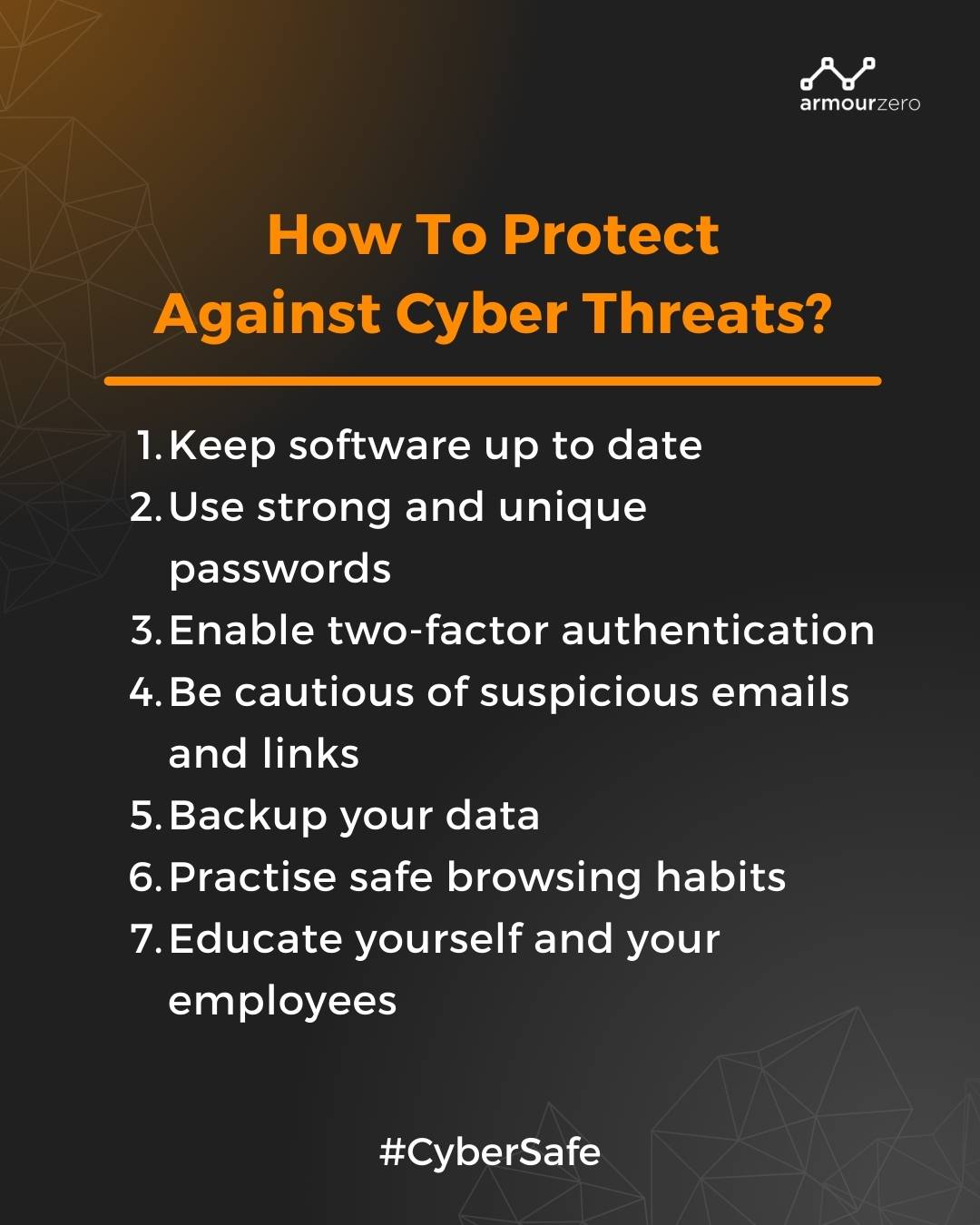
How To Protect Against Cyber Threats?
To protect against cyber threats requires a proactive and multi-layered approach. Here are some essential steps to enhance your cybersecurity defences:
-
Keep software up to date
Hackers frequently access your systems using flaws in out-of-date software. Therefore, regularly update your operating systems, applications, and security software to ensure they have the latest patches and security fixes.
-
Use strong and unique passwords
One of the easiest ways for cybercriminals to access your online accounts is through weak passwords. Make sure you and your staff use secure passwords that are a combination of letters, numbers, and symbols. Create strong passwords that are difficult to guess and use different passwords for each online account and consider using a password manager to securely store and manage your passwords.
-
Enable two-factor authentication (2FA)
Enable 2FA whenever possible to add an extra layer of security to your accounts. This typically involves a combination of a password and a second verification method, such as a code sent to your mobile device. Two-factor authentication (2FA) adds an extra layer of security to your online accounts by requiring users to provide an additional form of authentication, such as a verification code sent to a mobile device or email address.
-
Be cautious of suspicious emails and links
Exercise caution when opening emails, especially from unknown senders, and avoid clicking on suspicious links or downloading attachments that may contain malware or lead to phishing websites.
-
Backup your data
Regularly backup your important files and data to an external storage device or cloud-based service. This helps protect against data loss in case of ransomware attacks or hardware failures. Backup your important data regularly to minimise the impact of a data breach or cyberattack. The backup should be done online or offline such as a hard drive, USB stick, etc.
-
Practise safe browsing habits
Be cautious when visiting websites, especially those that are unfamiliar or known for hosting malicious content. Avoid downloading files from untrusted sources and use browser extensions that provide additional security. Try to use URL or DNS Filter to protect your website.
-
Educate yourself and your employees
Stay informed about the latest cybersecurity threats and best practices. Conduct cybersecurity awareness training to educate employees about potential risks, phishing techniques, and the importance of maintaining strong security practices.
Always remember that cybersecurity is an ongoing effort that requires continuous monitoring, updates, and adaptation to evolving threats. By following these measures and staying vigilant, you can significantly reduce the risk of falling victim to cyber threats and protect your digital assets.
Protect your organisation from cybercrime and cyber threats today with just one click!
See our pricing here and request a demo to understand further.
You can also contact our sales to help you choose the right cybersecurity services for your business.
![]()
Written by:
Fanny Fajarianti (Performance Marketing). Experienced digital marketer in the information technology and services industry.
I am text block. Click edit button to change this text. Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
Share this post
Related Posts

Earth Day: The Connection of Cybersecurity and Sustainability
- 22 Apr 2024
- By:Fanny Fajarianti
- Category: ArmourHacks
Uncover the link between Earth Day and Cybersecurity, promoting sustainability through data protection and environmental stewardship. Let’s secure a greener future.

What is DevSecOps? Definition & Best Practices for Tech Industries
- 18 Apr 2024
- By:Bernadetta Septarini
- Category: ArmourHacks
Learn about DevSecOps, principles, and best practices for the tech industry. Integrate security seamlessly into software development and enhance quality.

Safeguarding Your Organisation During the Hari Raya Holiday
- 09 Apr 2024
- By:Bernadetta Septarini
- Category: ArmourHacks
Protect your organisation from holiday cyberattacks during Hari Raya. Learn more about the risks and best practices for holiday security with ArmourZero.

Cyberattacks: A Growing Threat to Higher Education
- 02 Apr 2024
- By:Fanny Fajarianti
- Category: ArmourHacks
Universities hold sensitive data but face cyberattack risks in the digital age. Explore the impact of cyberattack and learn how to protect your institution.

