Spoofing vs Phishing:
Definition, Differences & Prevention

Spoofing and phishing are two frequently used methods by malicious actors in the constantly changing world of cyber threats. Both strategies aim to trick users into providing sensitive information to third parties without authorisation or to compromise systems. For individuals and organisations to be protected from cyberattacks, it is essential that they understand the definitions and distinctions between spoofing and phishing. In this article, we will explore what spoofing and phishing are, their key distinctions, and essential tips to prevent these threats.
What is spoofing in cybersecurity?
In cybersecurity, spoofing is a deceptive cyberattack method where attackers manipulate data across communication channels like emails, websites, or caller IDs to impersonate a trusted source, leading victims to mistakenly engage with them. This technique aims to create a false sense of legitimacy, making individuals believe they are interacting with a trustworthy entity, while in reality, they are being targeted by malicious actors.
How do hackers use spoofing?
Hackers use spoofing techniques to gain unauthorised access, steal data, or carry out other malicious activities by tricking their targets and manipulating different communication channels. Spoofing attacks take many forms, common types of spoofing attacks include:
-
Email Spoofing
Email spoofing is a form of cyberattack where hackers manipulate the sender’s email address, presenting themselves as familiar or trustworthy contacts. This is achieved by altering the “From” field to mimic a trusted source or replicating the name and email address of a known contact.
This deceptive technique can even involve subtle changes, like substituting characters to create a visually convincing facade, known as a homograph attack. Often, these spoofed emails contain links to malicious sites or infected attachments, and hackers may employ social engineering tactics to coax recipients into revealing personal or sensitive data.
The goal is to deceive recipients into thinking they are engaging with a legitimate source, enabling hackers to exploit human trust and manipulate victims into compromising actions, such as opening harmful attachments or sharing confidential information.
-
Caller ID Spoofing
Caller ID spoofing, similar to email spoofing, involves manipulating displayed phone numbers to appear familiar. Attackers frequently adopt the guise of customer support agents and employ social engineering tactics to extract sensitive data, such as social security numbers, birthdates, banking information, and passwords, when the recipient answers the call.
In more sophisticated instances, calls may be rerouted through international or long-distance carriers, resulting in exorbitant charges for the victim. This technique, known as vishing or voice phishing, capitalises on the modified caller ID information to create a false aura of trustworthiness, luring victims into divulging confidential information.
-
Website or Domain Spoofing
Domain spoofing is when an attacker creates a website that closely imitates an existing site, often through subtle domain name alterations. The intention is to trick users into attempting to log in, allowing the attacker to gather account credentials and personal data. Subsequently, these pilfered credentials can be utilised on trustworthy sites or sold for profit.
Frequently, website spoof attacks are initiated by email spoofing, wherein the attacker uses a fabricated email account to guide users to the counterfeit website. These malicious sites, bearing striking resemblance to authentic ones, are engineered to entice users into disclosing sensitive information like login details or payment particulars, which the hackers then seize and exploit.
-
IP Spoofing
The attackers use IP address changes to spoof or hide their real identities or impersonate different users, a method that is often used by serious adversaries in modern times Denial of Service (DoS). In this case, the attackers change their IP address to flood the victim’s website with traffic, thus restricting access to legitimate users. This method is one DoS attack, where understanding the IP address is important.
IP spoofing involves hackers manipulating the source IP address of network packets to change their origin, allowing them to evade security measures, launch Distributed Denial of Service (DDoS) attacks or gain access to There is no authority in the system by getting in front of the trusted IP address.
Read more: Most Common Cyber Threats & How to Protect Against Them.
-
Address Resolution Protocol (ARP) Spoofing
ARP (Address Resolution Protocol) is used to connect IP addresses to MAC (Media Access Control) addresses to facilitate data transmission. In an ARP attack, the attacker creates a link between their MAC address and the network’s valid IP address, allowing the attacker to intercept data intended for the IP owner.
This technique is often used for data theft or fraud, and it extends to applications that are susceptible to denial of service (DoS), man-in-the-middle (MitM) or time-out attacks. By manipulating the ARP table in a local network, ARP spoofing allows hackers to bind their MAC address to an authorised IP address, giving them the ability to intercept network traffic, steal information or even to start the next attack.
How to detect spoofing
Spoofing can be sophisticated, so the key is to pay attention to the details and trust your instincts. Be wary of websites that don’t have a lock symbol or green bar, or URLs that start with HTTP instead of HTTPS, the encrypted form of HTTP. Another way to tell a fake website is if your password manager doesn’t fill in your ID, indicating that it doesn’t recognise the website.
When checking emails, it’s important to pay close attention to the sender’s address, as scammers often use fake domains and real domains. In addition, grammatical inconsistencies, incorrect spellings, and unusual sentence structures indicate potential fraud. If in doubt, copying and pasting the content of the email into a Google search can reveal any scams that exist. For security reasons, it’s a good idea to hover over embedded links to preview the URL before clicking. Also paying attention to between an uppercase letter “I” (I) and a lowercase letter “l” (l), can also help detect fraud.
What does phishing mean?
Phishing refers to a type of cyberattack where criminals use fake communications, usually in the form of emails, messages or websites, to trick individuals into disclosing sensitive information, such as login credentials, financial details or personal data.
The attackers disguise themselves as legitimate and trustworthy companies, trying to trick recipients into doing certain things, such as clicking on malicious links, downloading infected files, or sharing confidential information. Phishing attacks exploit human psychology and trust to manipulate victims, which can lead to identity theft, financial loss, or unauthorised access to accounts or systems. There are four most common types of phishing, such as:
-
Spear phishing
Spear phishing is a targeted method, which targets specific individuals or groups. The attacker uses structured communications to carry out this attack, often using malicious emails. The purpose is to manipulate recipients into releasing sensitive information or providing unauthorised access without their knowledge.
-
Whale phishing
Whale phishing attacks focus on valuable targets, including senior executives or C-level employees. These attacks aim to remove money, sensitive data, or access the victim’s computer. A successful whaling attack can provide a springboard for new cyberattacks.
-
Voice phishing (vishing)
Voice phishing or vishing uses the phone system to do phishing. Attackers use voice calls to trick targets into revealing confidential information or performing security-compromising actions. This process makes voice communication exploiting human trust.
-
SMS phishing (smishing)
SMS phishing or smishing works through SMS messages, exploiting the trust of mobile users. These messages often contain deceptive content, tricking recipients into websites where malicious software or content awaits them. The goal is to trick users into entering harmful content.
These various phishing techniques use human behaviour, trust, and technical vulnerabilities to trick targets into compromising their security, revealing sensitive information, or engaging in actions that further the attacker’s goals. Therefore, surveillance, cybersecurity awareness, and caution in digital communications are important defences against victims of this system.
What is the difference between spoofing and phishing?
The terms “spoofing” and “phishing” are often used interchangeably, but they mean different things. Spoofing uses fake email addresses, screen names, phone numbers, or web addresses to trick people into believing they are dealing with a reputable and trusted source. While phishing tricks you into providing personal data that can be used for identity theft. Many phishers use tricks to trick people into thinking that they are providing personal information to legitimate and trustworthy sources.
Moreover, spoofing and phishing have distinct characteristics, such as:
Focus:
Spoofing focuses on deceiving the victim about the identity or source of communication (e.g., email, website, or IP address).
Phishing concentrates on manipulating the victim into taking certain actions or divulging sensitive information.
Method:
Spoofing involves altering data or information to mislead the victim.
Phishing relies on social engineering tactics and psychological manipulation to trick the victim.
Goal:
The primary goal of spoofing is to impersonate a trusted entity and gain unauthorised access or hide the attacker’s identity.
The main goal of phishing is to obtain sensitive information, such as login credentials or financial data, or to deliver malware to the victim’s system.
How to prevent phishing and spoofing?
To defend against spoofing and phishing attacks, individuals and organisations can implement the following preventive measures:
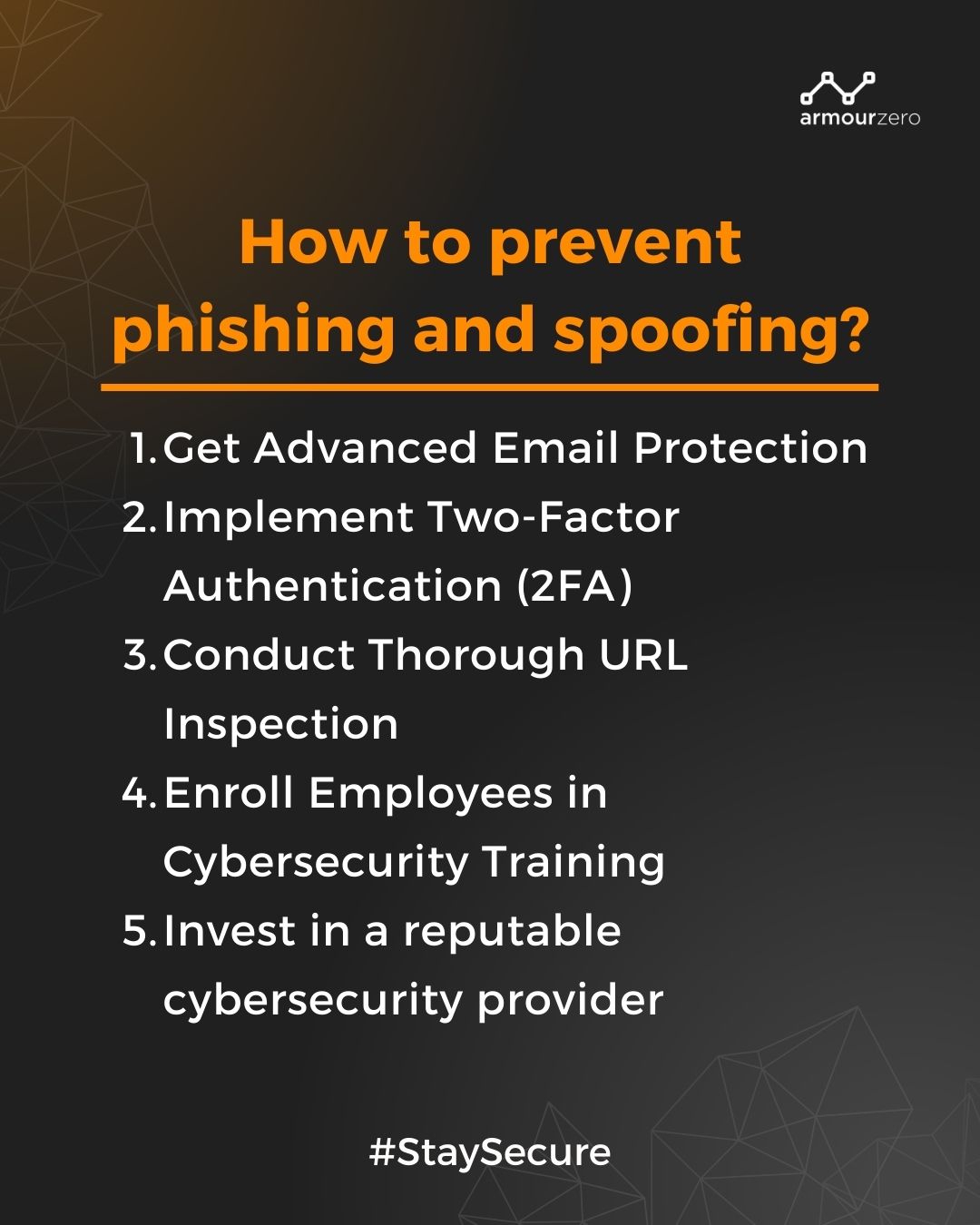
1. Email protection
Utilise email protection to filter spam email and prevent spoofed email landing in your inbox.
2. Two-factor authentication (2FA)
Implement 2FA for sensitive accounts and services to add an extra layer of security and protect against unauthorised access.
3. URL inspection
Before clicking on links received via email or other sources, hover the mouse pointer over the link to check the destination URL. Avoid clicking on suspicious or shortened URLs.
4. Employee training
Conduct regular cybersecurity awareness training for employees to recognise and avoid phishing attempts. Educate them about common phishing techniques and how to verify the legitimacy of emails and websites.
5. Invest in a reputable cybersecurity provider
Spoofing and phishing can cause harm to your organisation, therefore it is important to invest in a reputable cybersecurity provider that will alert you about potential threats, stop downloads, and prevent malware from taking over.
Conclusion
Spoofing and phishing are dangerous cyberattack methods that exploit human vulnerabilities and trust in digital communications. Knowing their definitions and differences is important for individuals and organisations to be vigilant and take security measures to protect against these threats. By being informed and adopting best practices for online security, we can arm ourselves against the pervasive threat of identity theft and phishing attacks.
Protect your organisation from spoofing and phishing today with just one click!
See our pricing here and request a demo to understand further.
You can also contact our sales to help you choose the right cybersecurity services for your business.
![]()
Written by:
Fanny Fajarianti (Performance Marketing). Experienced digital marketer in the information technology and services industry.
Share this post
Related Posts

Earth Day: The Connection of Cybersecurity and Sustainability
- 22 Apr 2024
- By:Fanny Fajarianti
- Category: ArmourHacks
Uncover the link between Earth Day and Cybersecurity, promoting sustainability through data protection and environmental stewardship. Let’s secure a greener future.

What is DevSecOps? Definition & Best Practices for Tech Industries
- 18 Apr 2024
- By:Bernadetta Septarini
- Category: ArmourHacks
Learn about DevSecOps, principles, and best practices for the tech industry. Integrate security seamlessly into software development and enhance quality.

Safeguarding Your Organisation During the Hari Raya Holiday
- 09 Apr 2024
- By:Bernadetta Septarini
- Category: ArmourHacks
Protect your organisation from holiday cyberattacks during Hari Raya. Learn more about the risks and best practices for holiday security with ArmourZero.

Cyberattacks: A Growing Threat to Higher Education
- 02 Apr 2024
- By:Fanny Fajarianti
- Category: ArmourHacks
Universities hold sensitive data but face cyberattack risks in the digital age. Explore the impact of cyberattack and learn how to protect your institution.

